write certificate to smart card by default, importing a P12 file is forbidden if the CSP is “Microsoft Base Smart Card Crypto Provider” . Set the following keys to disable this protection : If this tweak is not applied, the import fails in CryptImportKey with the return code NTE_BAD_TYPE (0x8009000A) .reg file : See more NFC Tools is a cross platform app that works on Android, iOS, MacOS, Windows and Linux. . With this device plugged in I get "Unable to connect NFC reader." The reader is working for .
0 · smart card log on 1.3.6.1.4.1.311.20.2.2
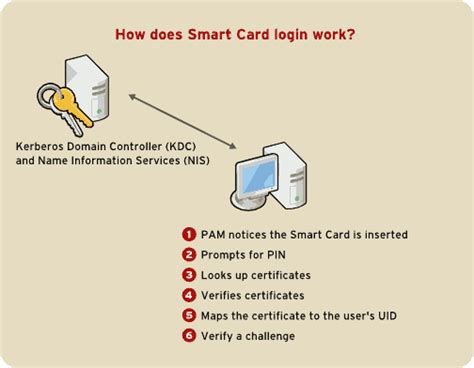
1 · smart card certificate authentication
2 · smart card authentication step by
3 · install smart card certificates
4 · import certificates from smart card
5 · export certificate from smart card
6 · enable smart card authentication
7 · add certificate to credential manager
The hub for all your updates on My Nintendo. Earn points by playing apps on your smart .IC/ID RFID Reader Writer: NFC Reader Writer Scanner for 125khz/13.56Mhz Cards, Support Cracking IC Encrypted Cards, Driver-Free, LED Light Prompt,and USB Full Speed Interface with Software . IC/ID English 10 Frequency RFID Decoder Handheld NFC Scanner for 125Khz .
smart card log on 1.3.6.1.4.1.311.20.2.2
rfid protection como funciona
Open a command line and type “certutil -SCInfo”. Look at the line name “card”. In this example, it is “ePass2003” Note : if the smart card contains already some cryptographic material, for each container, a line named “Provider” is added. This line contains the name of the CSP required. You can skip the next step. See moreLaunch regedit.exe and open HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\Calais\SmartCards Open the subkey named as the name of the smart card. Look at the key “Crypto Provider” to get the name of the CSP See moreby default, importing a P12 file is forbidden if the CSP is “Microsoft Base Smart Card Crypto Provider” . Set the following keys to disable this protection : If this tweak is not applied, the import fails in CryptImportKey with the return code NTE_BAD_TYPE (0x8009000A) .reg file : See more Have you thought about moving a certificate including its (exportable) keys from a user's profile into a smart card? There are three simple steps required to do this if the .
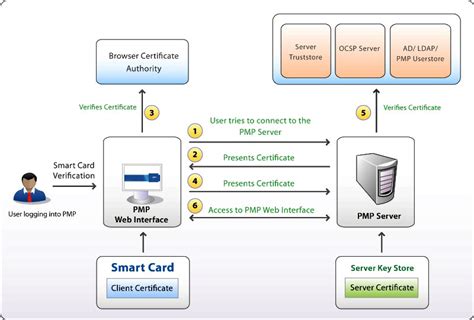
In this article we have covered the basics of Certificate-Based Authentication (CBA) using a smart card or a YubiKey (as a smart card). We have learned that CBA uses a .
For sign-in to work in a smart card-based domain, the smart card certificate must meet the following conditions: The KDC root certificate on the smart card must have an HTTP . The first and perhaps only difficult task (not so much since you now have a guide!) is to generate a certificate with the correct object identifiers (OID’s) to support smart card logon . Generating and importing user certificates as a .pfx file. In environments where the user certificates cannot be generated on the YubiKey, they can be generated on a Windows . Applies to: Windows 11, Windows 10, Windows Server 2025, Windows Server 2022, Windows Server 2019, Windows Server 2016. This topic for the IT professional and .
Step 1: Create the certificate template. Step 2: Create the TPM virtual smart card. Step 3: Enroll for the certificate on the TPM Virtual Smart Card. Important. This basic .
6.1. Creating local certificates. Copy link. Follow this procedure to perform the following tasks: Generate the OpenSSL certificate authority. Create a certificate signing request. Warning. The .PC/SC wrapper classes for .NET, written in C#. The package contains classes to access the Personal Computer/Smart Card Resource Manager using the system's native PC/SC API. Implements partial ISO7816 support. The library is written to run on both, Windows and Unix (Linux with Mono using PCSC Lite). 1. Certificates on smartcards are usually accessed via PKCS#11 API (cross-platform way) and on Windows they can be accessed via Windows Certificate Store. As mentioned in comments, Java supports both ways natively, though there exist some restrictions/bugs in Java providers. Access to the certificates themselves, though, is not .
smart card certificate authentication
2. From smart card point of view, a X.509 certificate is just a binary file, but one needs to find and address the correct file, a functionality provided by the PKCS#11 support for the card. While the following link is for a thin python layer on top of pkcs #11, the last example may serve as starting point for C# also. There are several solutions which you can use to communicate with your smart card via this library. Such as: pkcs11-tool (CLI interface), PyKCS11 (python wrapper). Here is an example how it could be achieved with PyKCS11: from asn1crypto import x509. from PyKCS11 import *. pkcs11 = PyKCS11Lib() Now I am developing a c# application that can access the USB Reader with the card, retrieve the certificate and sign an XML. The ideal solution is to "copy" the certificate inside an X509Certificate2 object. I'm using this code right now: List certificates = new List(); CspParameters cspParameters = new . Public key extraxction. If you already have exported the certificate, it is probably easier to extract the public key from there, instead of from the smartcard. You can use openssl for that: openssl x509 -in cert.pem -pubkey -out pubkey.pem -noout.
Microsoft Base Smart Card Crypto Provider Microsoft Smart Card Key Storage Provider I have tried both of those in the below script with the same end result. The second of which gives me characters when the script tells me what my default user key container is, so I have a feeling that it is not correct.
User clicks on the login button: "Login with smart card"; The system reads the card using some reader or build in reader to the laptop (let's say it wait 5 seconds for the user to use the card) The system authenticates the user with AD; The smart card contains both the public and the private key. Can and if yes, how this could be achieved? CertPropSvc is notified that a smart card was inserted. CertPropSvc reads all certificates from all inserted smart cards. The certificates are written to the user's personal certificate store. So yes, gnerally certificates should pop up in User Personal Certificate Store automatically. First thing to check is that you have CertPropSvc service .
On Windows (2000, XP, and Vista) any time you insert your smartcard into a smartcard reader all the certificates on it are propogated to your personal certificate store. Your private key stays on your smart card. What that means is if you use your certificate (for example to digitally sign an e-mail) then you are prompted to insert your smart card.PC/SC wrapper classes for .NET, written in C#. The package contains classes to access the Personal Computer/Smart Card Resource Manager using the system's native PC/SC API. Implements partial ISO7816 support. The library is written to run on both, Windows and Unix (Linux with Mono using PCSC Lite). 1. Certificates on smartcards are usually accessed via PKCS#11 API (cross-platform way) and on Windows they can be accessed via Windows Certificate Store. As mentioned in comments, Java supports both ways natively, though there exist some restrictions/bugs in Java providers. Access to the certificates themselves, though, is not . 2. From smart card point of view, a X.509 certificate is just a binary file, but one needs to find and address the correct file, a functionality provided by the PKCS#11 support for the card. While the following link is for a thin python layer on top of pkcs #11, the last example may serve as starting point for C# also.
There are several solutions which you can use to communicate with your smart card via this library. Such as: pkcs11-tool (CLI interface), PyKCS11 (python wrapper). Here is an example how it could be achieved with PyKCS11: from asn1crypto import x509. from PyKCS11 import *. pkcs11 = PyKCS11Lib() Now I am developing a c# application that can access the USB Reader with the card, retrieve the certificate and sign an XML. The ideal solution is to "copy" the certificate inside an X509Certificate2 object. I'm using this code right now: List certificates = new List(); CspParameters cspParameters = new .
Public key extraxction. If you already have exported the certificate, it is probably easier to extract the public key from there, instead of from the smartcard. You can use openssl for that: openssl x509 -in cert.pem -pubkey -out pubkey.pem -noout. Microsoft Base Smart Card Crypto Provider Microsoft Smart Card Key Storage Provider I have tried both of those in the below script with the same end result. The second of which gives me characters when the script tells me what my default user key container is, so I have a feeling that it is not correct. User clicks on the login button: "Login with smart card"; The system reads the card using some reader or build in reader to the laptop (let's say it wait 5 seconds for the user to use the card) The system authenticates the user with AD; The smart card contains both the public and the private key. Can and if yes, how this could be achieved? CertPropSvc is notified that a smart card was inserted. CertPropSvc reads all certificates from all inserted smart cards. The certificates are written to the user's personal certificate store. So yes, gnerally certificates should pop up in User Personal Certificate Store automatically. First thing to check is that you have CertPropSvc service .
Try the Tag Reader in Control Center. If your iPhone isn’t automatically recognizing NFC tags, you can try using the NFC Tag Reader tool that’s built into your iPhone. However, this is only .
write certificate to smart card|export certificate from smart card