public-key-enabled smart card Your PIV/CAC credential contains an authentication certificate key pair (public and private) for smart card logon. Using a PIV/CAC key pair is very similar to using a self-signed key pair for SSH. Custom Hand Made FEW 15PCS/12PCS NFC Amiibo Card Fast Shipping! Free .
0 · Using SSH Public Key Authentication with a Smart
1 · Smart Cards and the Kerberos Protocol
2 · Smart Card Logon for SSH
Open the payment app and add a credit or debit card. Step 3.1. Choose the default payment app on your Android device. Step 3.2. Choose the default payment app on your Samsung Galaxy. Step 4. Turn on NFC on your .Touch the WRITE TAG (AUTO) button and press your NTAG215 NFC tag to your Android device. The stickers aren't re-writeable so I'd advise against trying that in the future so you don't mess the sticker up. Another ntag215 tag I recommend .Custom Animal Crossing Amiibo Cards. ALL Series are Available in our store. Fast Ship from .
The idea is simple: Public Key Authentication for SSH is well documented, I just want my private key to live on my hardware token instead of being a file on my hard drive. Thanks to my job, I already had (some) .Your PIV/CAC credential contains an authentication certificate key pair (public and private) for . The idea is simple: Public Key Authentication for SSH is well documented, I just want my private key to live on my hardware token instead of being a file on my hard drive. Thanks to my job, I already had (some) experience with OpenSSL, OpenSC, PKCS#11 and PKCS#15 , and it's not like these technology are new, so I was expecting it would be .
Your PIV/CAC credential contains an authentication certificate key pair (public and private) for smart card logon. Using a PIV/CAC key pair is very similar to using a self-signed key pair for SSH.To enable authentication using a smart card on a remote server, you need to transfer the public key (smartcard.pub) retrieved in the previous step (in the OpenSSH format) to the remote server. You can do it by simply copy paste to remote shell, or by using ssh-copy-id : Extract and install the public key on the SSH server. Use ssh-keygen to extract the user’s public key from the smart card and store it in a file format usable by ssh.
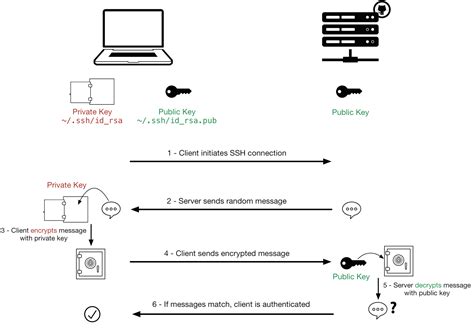
One of the authentication methods supported by the SSH protocol is public key authentication. A public key is copied to the SSH server where it is stored and marked as authorized. The owner of the corresponding private key in the smart card can then SSH login to the server. How public key authentication works. In its most simple form, public key authentication as follows: The server sends Alice a random string (nonce). Alice encrypts the nonce with her private key and sends it to the server along with her certificate.
PKI, or public key infrastructure, encompasses everything used to establish and manage public key encryption. This includes software, hardware, policies, and procedures that are used to create, distribute, manage, store, and revoke digital certificates. A digital certificate cryptographically links a public key with the device or user who owns it.FIPS 201 Approved Smart Card (AAL3) Common PIV-I Certificates The Common PIV-I card contains up to five certificates with four available to the Common PIV-I card holder.PDF. To configure smart card authentication with local certificates: The host is not connected to a domain. You want to authenticate with a smart card on this host. You want to configure SSH access using smart card authentication. You want to configure the smart card with authselect. Use the following configuration to accomplish this scenario:
Using SSH Public Key Authentication with a Smart
This is a step-by-step guide on setting up a YubiKey with PIV to work for public-key authentication with OpenSSH through PKCS #11. These instructions apply primarily to macOS and Linux systems. The idea is simple: Public Key Authentication for SSH is well documented, I just want my private key to live on my hardware token instead of being a file on my hard drive. Thanks to my job, I already had (some) experience with OpenSSL, OpenSC, PKCS#11 and PKCS#15 , and it's not like these technology are new, so I was expecting it would be .Your PIV/CAC credential contains an authentication certificate key pair (public and private) for smart card logon. Using a PIV/CAC key pair is very similar to using a self-signed key pair for SSH.To enable authentication using a smart card on a remote server, you need to transfer the public key (smartcard.pub) retrieved in the previous step (in the OpenSSH format) to the remote server. You can do it by simply copy paste to remote shell, or by using ssh-copy-id :
Extract and install the public key on the SSH server. Use ssh-keygen to extract the user’s public key from the smart card and store it in a file format usable by ssh.One of the authentication methods supported by the SSH protocol is public key authentication. A public key is copied to the SSH server where it is stored and marked as authorized. The owner of the corresponding private key in the smart card can then SSH login to the server.
How public key authentication works. In its most simple form, public key authentication as follows: The server sends Alice a random string (nonce). Alice encrypts the nonce with her private key and sends it to the server along with her certificate.
PKI, or public key infrastructure, encompasses everything used to establish and manage public key encryption. This includes software, hardware, policies, and procedures that are used to create, distribute, manage, store, and revoke digital certificates. A digital certificate cryptographically links a public key with the device or user who owns it.FIPS 201 Approved Smart Card (AAL3) Common PIV-I Certificates The Common PIV-I card contains up to five certificates with four available to the Common PIV-I card holder.PDF. To configure smart card authentication with local certificates: The host is not connected to a domain. You want to authenticate with a smart card on this host. You want to configure SSH access using smart card authentication. You want to configure the smart card with authselect. Use the following configuration to accomplish this scenario:
Smart Cards and the Kerberos Protocol

swr smart card lost
swivel card smart business cards
$32.74
public-key-enabled smart card|Smart Card Logon for SSH