rfid security tag RFID security tags are the simplest way for your business to keep track of inventory, shipments, and protect against theft. Small, inexpensive, and effective, if you don’t currently use them then you need to seriously reconsider! This article will explain what they are, how they work, and where they can be used. Install the NFC reader into the mounted bracket. Route the cable to where the GO device is planned to be secured. Ensure the harness does not interfere with any moving parts. . Hereby, Geotab (Address: 2440 Winston .GO NFC Logger. Versatile Temperature Recorder GO NFC Loggers monitor time and .
0 · two types of rfid tags
1 · rfid tags and their uses
2 · rfid radio frequency identification tags
3 · rfid privacy and security issues
4 · retail anti theft security tags
5 · radio frequency identification tags are
6 · problems with rfid technology
7 · problems with rfid
$35.96
RFID tags come in three main types—passive, active, and semi-passive—each with distinct ranges, power sources, and use cases. RFID technology revolutionizes asset tracking . RFID security tags are the simplest way for your business to keep track of inventory, shipments, and protect against theft. Small, inexpensive, and effective, if you don’t currently use them then you need to seriously reconsider! This article will explain what they are, how they work, and where they can be used. RFID tags come in three main types—passive, active, and semi-passive—each with distinct ranges, power sources, and use cases. RFID technology revolutionizes asset tracking and fixed inventory management by providing real-time .
A simple introduction to how RF and RFID tags are used in smart cards, toll collection, shop security, and other everyday applications.
What Are RF Security Tags? These tags are small devices that inform a shop's employees of when someone enters or exits with the tag on them. RF security tags are thus used to ensure specific products are safe from theft. Their activation also proves that an individual has stolen the item rather than bought it. A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and reader don't have to touch. Some RFID tags can be powered by a .RFID tag range refers to the maximum distance at which an RFID reader can effectively read the tag’s information. This range is influenced by several factors, including the type of tag, the power of the reader, and environmental conditions.
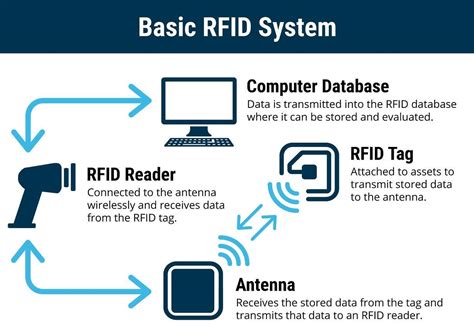
RFID tags are small electronic devices that store information and communicate with other devices using radio waves. RFID tags are used in a variety of applications, from tracking inventory to monitoring the movements of livestock.Sensormatic Solutions' line of Hard Tags offer a variety of security tags available in AM, RF, RFID, and dual technologies to improve loss prevention.An RFID security tag system consists of passive or active RFID tags that communicate with RFID readers via radio waves that track and identify tagged items. The system consists of two components: an RFID reader and the label or tag. Most RFID security tags are passive, but whether you opt for ultrahigh-frequency (UHF) tags, which are compliant with the EPC Gen 2 standard, or high-frequency (HF) tags, typically ISO-compliant, will depend on what’s critical to your value chain.
RFID security tags are the simplest way for your business to keep track of inventory, shipments, and protect against theft. Small, inexpensive, and effective, if you don’t currently use them then you need to seriously reconsider! This article will explain what they are, how they work, and where they can be used.
two types of rfid tags

RFID tags come in three main types—passive, active, and semi-passive—each with distinct ranges, power sources, and use cases. RFID technology revolutionizes asset tracking and fixed inventory management by providing real-time . A simple introduction to how RF and RFID tags are used in smart cards, toll collection, shop security, and other everyday applications.
convert cdc card to smart health card
What Are RF Security Tags? These tags are small devices that inform a shop's employees of when someone enters or exits with the tag on them. RF security tags are thus used to ensure specific products are safe from theft. Their activation also proves that an individual has stolen the item rather than bought it. A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and reader don't have to touch. Some RFID tags can be powered by a .RFID tag range refers to the maximum distance at which an RFID reader can effectively read the tag’s information. This range is influenced by several factors, including the type of tag, the power of the reader, and environmental conditions.
RFID tags are small electronic devices that store information and communicate with other devices using radio waves. RFID tags are used in a variety of applications, from tracking inventory to monitoring the movements of livestock.Sensormatic Solutions' line of Hard Tags offer a variety of security tags available in AM, RF, RFID, and dual technologies to improve loss prevention.An RFID security tag system consists of passive or active RFID tags that communicate with RFID readers via radio waves that track and identify tagged items. The system consists of two components: an RFID reader and the label or tag.
rfid tags and their uses

rfid radio frequency identification tags

continuous prompts to enter smart card pin windows 10
commonwealth bank smart access debit card
Android provides generic support for these use cases with the android.nfc.tech package, which is described in Table 1. You can use the getTechList() method to determine .
rfid security tag|problems with rfid