msds-expire-passwords-on-smart-card-only-accounts The attribute: ms-DS-Expire-Passwords-On-Smart-Card-Only-Accounts is a domain level configuration. The password is automatically changed on the “smart card only” user accounts . The ACS ACR39U-NF PocketMate II is a FIPS 201 compliant USB-C smart card reader. With a .I believe the chips communicate via NFC, so would think that it should be possible for an NFC enabled smartphone to detect this. That would .
0 · [MS
1 · Expire Passwords On Smart Card Only Accounts
2 · Automatically change passwords for accounts that require login vi
3 · "msDS
In the example above “your.uniqueapp.nfc” can be “com.your.package.name.nfc”. The idea of having a unique Mime Type on the NFC tags is to prevent the device from having to choose between launching .
[MS
rfid scanner shield
This attribute controls whether the passwords on smart-card-only accounts expire in accordance with the password policy. cn: ms-DS-Expire-Passwords-On-Smart-Card-Only-Accounts. lDAPDisplayName: msDS-ExpirePasswordsOnSmartCardOnlyAccounts. ."msDS-ExpirePasswordsOnSmartCardOnlyAccounts not exist" error when you check domai.The attribute: ms-DS-Expire-Passwords-On-Smart-Card-Only-Accounts is a domain level configuration. The password is automatically changed on the “smart card only” user accounts . This attribute controls whether the passwords on smart-card-only accounts expire in accordance with the password policy. cn: ms-DS-Expire-Passwords-On-Smart-Card-Only-Accounts. lDAPDisplayName: msDS-ExpirePasswordsOnSmartCardOnlyAccounts. attributeID: 1.2.840.113556.1.4.2344.
"msDS-ExpirePasswordsOnSmartCardOnlyAccounts not exist" error when you check domain object properties by using RSAT in Windows 10 - Microsoft Support. Applies To. Symptoms. You have a Windows 10, version 1607-based or a Windows 10, version 1809-based client that joins a domain with a Windows Server 2008 R2 or Windows Server 2012 R2 controller.
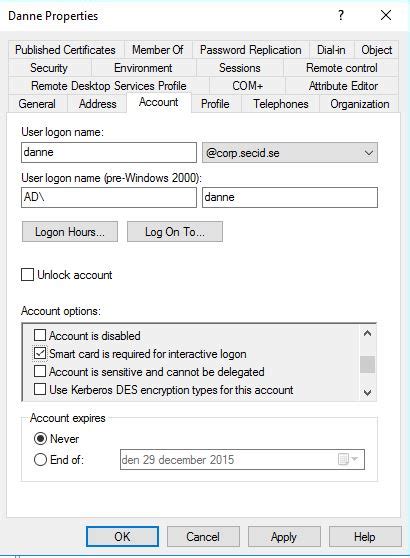
The attribute: ms-DS-Expire-Passwords-On-Smart-Card-Only-Accounts is a domain level configuration. The password is automatically changed on the “smart card only” user accounts according to the password policy.If you have enrolled a smart card to a user, you have the option to configure if the user is required to use a smart card or if he will be allowed to use a password. On the user account you can set the flag: SMARTCARD_REQUIRED – 0x40000 in the userAccountControl attribute.dn: CN=ms-DS-Expire-Passwords-On-Smart-Card-Only-Accounts,CN=Schema,CN=Configuration,DC=X changetype: ntdsSchemaAdd objectClass: attributeSchema CN: ms-DS-Expire-Passwords-On-Smart-Card-Only-Accounts attributeID: 1.2.840.113556.1.4.2344 attributeSyntax: 2.5.5.8 adminDisplayName: ms-DS-Expire . From my research, this is the easiest way to update the NT hash for the account - The only other way I've found is to use the attribute ms-DS-Expire-Passwords-On-Smart-Card-Only-Accounts so that the hash is updated when the password expires (can set to whatever interval you want), but that requires a functional domain level of 2016, which is .
All of our users are issued smart cards to log onto their systems and smart card logon is working properly in both domains but there's a small difference when it comes to account password behavior. In both domains we configure user accounts with the following: SmartCardLogonRequired : True. PasswordNeverExpires : False.
Here's a script that runs on a specific OU and gets username, email, dn, password last set, expiry computed and days in the password will expire in. Skips any users that has Pass never expire enabled. The UserAccountControl attribute can be used to configure several account settings in Active Directory. This applies, for example, to the expiration date of passwords or to Kerberos delegation. An AD audit should check this attribute regularly. This can be done using PowerShell, and there is a cmdlet for changing flags.Expire Passwords On Smart Card Only Accounts. I was browsing thru the new schema updates in Windows Server TP 4 and found an interesting new attribute: ms-DS-Expire-Passwords-On-Smart-Card-Only-Accounts. Sch83.ldf:
Expire Passwords On Smart Card Only Accounts
This attribute controls whether the passwords on smart-card-only accounts expire in accordance with the password policy. cn: ms-DS-Expire-Passwords-On-Smart-Card-Only-Accounts. lDAPDisplayName: msDS-ExpirePasswordsOnSmartCardOnlyAccounts. attributeID: 1.2.840.113556.1.4.2344."msDS-ExpirePasswordsOnSmartCardOnlyAccounts not exist" error when you check domain object properties by using RSAT in Windows 10 - Microsoft Support. Applies To. Symptoms. You have a Windows 10, version 1607-based or a Windows 10, version 1809-based client that joins a domain with a Windows Server 2008 R2 or Windows Server 2012 R2 controller.The attribute: ms-DS-Expire-Passwords-On-Smart-Card-Only-Accounts is a domain level configuration. The password is automatically changed on the “smart card only” user accounts according to the password policy.If you have enrolled a smart card to a user, you have the option to configure if the user is required to use a smart card or if he will be allowed to use a password. On the user account you can set the flag: SMARTCARD_REQUIRED – 0x40000 in the userAccountControl attribute.
dn: CN=ms-DS-Expire-Passwords-On-Smart-Card-Only-Accounts,CN=Schema,CN=Configuration,DC=X changetype: ntdsSchemaAdd objectClass: attributeSchema CN: ms-DS-Expire-Passwords-On-Smart-Card-Only-Accounts attributeID: 1.2.840.113556.1.4.2344 attributeSyntax: 2.5.5.8 adminDisplayName: ms-DS-Expire .
From my research, this is the easiest way to update the NT hash for the account - The only other way I've found is to use the attribute ms-DS-Expire-Passwords-On-Smart-Card-Only-Accounts so that the hash is updated when the password expires (can set to whatever interval you want), but that requires a functional domain level of 2016, which is . All of our users are issued smart cards to log onto their systems and smart card logon is working properly in both domains but there's a small difference when it comes to account password behavior. In both domains we configure user accounts with the following: SmartCardLogonRequired : True. PasswordNeverExpires : False.
Here's a script that runs on a specific OU and gets username, email, dn, password last set, expiry computed and days in the password will expire in. Skips any users that has Pass never expire enabled. The UserAccountControl attribute can be used to configure several account settings in Active Directory. This applies, for example, to the expiration date of passwords or to Kerberos delegation. An AD audit should check this attribute regularly. This can be done using PowerShell, and there is a cmdlet for changing flags.
There is no need to use Password Protection, is independent from "Read Only" , but they could be combined if you would like to. The static lock bits can set the pages from 03h .
msds-expire-passwords-on-smart-card-only-accounts|[MS