security bit of tag rfid RFID tag encryption is a security technology used to protect data transmitted via radio frequency identification (RFID) technology. The main purpose of RFID tag encryption is to ensure that . To use amiibo cards or figures on the Nintendo Switch, simply press the amiibo against the device’s NFC reader. The NFC chip will be scanned, unlocking unique bonuses like characters, items, and .
0 · two types of rfid tags
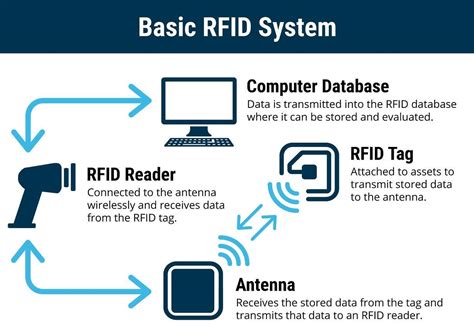
1 · rfid tags and their uses
2 · rfid radio frequency identification tags
3 · rfid privacy and security issues
4 · retail anti theft security tags
5 · radio frequency identification tags are
6 · problems with rfid technology
7 · problems with rfid
The business card option is designed to share your contact information with .
RFID tag encryption is a security technology used to protect data transmitted via radio frequency identification (RFID) technology. The main purpose of RFID tag encryption is to ensure that .

A lock password is a 32-bit password which must be transmitted before a tag will transmit its data. Skimmers will be unable to access the data since they can’t provide the password (a 32-bit password has 4,294,967,296 possible combinations).RFID tag encryption is a security technology used to protect data transmitted via radio frequency identification (RFID) technology. The main purpose of RFID tag encryption is to ensure that the data transmitted between the tag and the reader is not read or .
Someone with specific tools and enough knowledge on RFID (including complete documentation) could analyze the working frequency of an RFID tag and then decode the data or perform an attack such as cloning the RFID or doing a Denial-of-Service attack.
RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by attackers to exploit RFID vulnerabilities. Security issues in RFID system. The RFID scheme consists of several classes of tags and reader. These tags include an inadequate amount of memory and low-power capacity. However, there are numerous other issues in terms of .Besides being vulnerable to common attacks such as eavesdropping, man-in-the-middle, and denial of service, RFID technology is, in particular, susceptible to spoofing and power attacks (Figure 2). This section illustrates different kinds of attacks and provides countermeasures against these attacks. Fig. 2.
Like any other security devices and mechanism RFID is not flawless. Despite its widespread application and usage, RFID poses security threats and challenges that need to be addressed properly before deployment. This post aims to highlight several important RFID .In this paper, some of the latest technical research on privacy and security problems has been investigated in radio-frequency identification and security bit method, and it has been shown that in order to achieve this level of individual security, multiple technologies of RFID security development should combine with each other.The switching operation of the tag security bit requires an authorization system through a special RFID tag. An RFID tag reader can monitor tags in two public and private modes. When the security bit is on, the tag will respond to the scan in a private mode.
topic explores new methods for enforcing security in the actual transfer of tags, protecting the privacy of the parts and exploring the scalability of the process to secondhand markets and . A lock password is a 32-bit password which must be transmitted before a tag will transmit its data. Skimmers will be unable to access the data since they can’t provide the password (a 32-bit password has 4,294,967,296 possible combinations).RFID tag encryption is a security technology used to protect data transmitted via radio frequency identification (RFID) technology. The main purpose of RFID tag encryption is to ensure that the data transmitted between the tag and the reader is not read or . Someone with specific tools and enough knowledge on RFID (including complete documentation) could analyze the working frequency of an RFID tag and then decode the data or perform an attack such as cloning the RFID or doing a Denial-of-Service attack.
RFID attacks occur when an unauthorized individual intercepts or manipulates the signals transmitted between RFID tags and readers. There are several techniques commonly used by attackers to exploit RFID vulnerabilities. Security issues in RFID system. The RFID scheme consists of several classes of tags and reader. These tags include an inadequate amount of memory and low-power capacity. However, there are numerous other issues in terms of .
two types of rfid tags
Besides being vulnerable to common attacks such as eavesdropping, man-in-the-middle, and denial of service, RFID technology is, in particular, susceptible to spoofing and power attacks (Figure 2). This section illustrates different kinds of attacks and provides countermeasures against these attacks. Fig. 2.Like any other security devices and mechanism RFID is not flawless. Despite its widespread application and usage, RFID poses security threats and challenges that need to be addressed properly before deployment. This post aims to highlight several important RFID .In this paper, some of the latest technical research on privacy and security problems has been investigated in radio-frequency identification and security bit method, and it has been shown that in order to achieve this level of individual security, multiple technologies of RFID security development should combine with each other.The switching operation of the tag security bit requires an authorization system through a special RFID tag. An RFID tag reader can monitor tags in two public and private modes. When the security bit is on, the tag will respond to the scan in a private mode.
nfc android phone tag
nfc cattle tags
rfid tags and their uses

rfid radio frequency identification tags
Go to the App Store. Search for “ NFC Tools.”. Once you’ve found the app, proceed with the installation. Upon launching the app, you’ll be greeted with a straightforward .
security bit of tag rfid|retail anti theft security tags