secure symmetric authentication for rfid tags ppt download Ø Numerous authentication protocols for RFID systems were proposed in an attempt to . NFC (Near Field Communication) technology is widely used for various purposes, such as contactless payments, data transfer between devices, and accessing information from .
0 · Securing IoT
1 · Secure symmetric authentication for RFID tags
2 · Secure Symmetric Authentication for RFID Tags
3 · Secure Symmetric Authentication for RFID Tags
4 · SECURE SYMMETRIC AUTHENTICATION FOR RFID TAGS
5 · Presentation On SECURE SYMMETRIC AUTHENTICATION
6 · (PPTX) Presentation On SECURE SYMMETRIC
NFC Reader is a simple and efficient tool letting you to read contact-less tags on your smartphones and tablets. NFC Reader supports various tags like NDEF, RFID, FeliCa, ISO 14443, Mifare Classic 1k, MIFARE .

Ø Numerous authentication protocols for RFID systems were proposed in an attempt to .The three main security threats in RFID systems are forgery of tags, unwanted tracking of .The three main security threats in RFID systems are forgery of tags, unwanted tracking of .
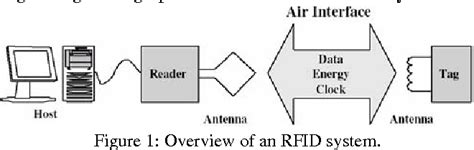
In this paper, we demonstrate how the project ART (Authentication for long-range RFID . Targeting RFID tag with short tag ID, we employ a resource friendly symmetric .Starting with a short introduction into common RFID systems with passive tags, we present a . Recently, many solutions were proposed to secure RFID systems and many .
The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.
Securing IoT
Ø Numerous authentication protocols for RFID systems were proposed in an attempt to prevent unauthorized tracking and monitoring, impersonation or cloning, and information leakage. Ø This paper enhances passive RFID tags with cryptographically secure authentication.The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners. Targeting RFID tag with short tag ID, we employ a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in active type RFID.
Starting with a short introduction into common RFID systems with passive tags, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications.
Secure symmetric authentication for RFID tags
Presentation On SECURE SYMMETRIC AUTHENTICATION FOR RFID TAGS DBS INSTITUTE OF TECHNOLOGY Kavali,SPSR Nellore Presented By K.Sandhya, 118T1A0433, ECE.Several authentication schemes have been proposed for providing security in RFID systems. Here, we give a brief review of some protocols. Albert et al.2 use three phases for authentication: initialization, identification (synchronised and desynchronised), and updating phase. This protocol uses the PRNGs to produce an unpredictable
Starting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. We demonstrate vulnerabilities of current RFID systems and explain how application of an authentication mechanism can solve them.
Recently, many solutions were proposed to secure RFID systems and many such systems are based on only lightweight primitives, including symmetric encryption, hash functions, and exclusive OR operation.The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.
Ø Numerous authentication protocols for RFID systems were proposed in an attempt to prevent unauthorized tracking and monitoring, impersonation or cloning, and information leakage. Ø This paper enhances passive RFID tags with cryptographically secure authentication.The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners.
tag 215 nfc stickers work with
Targeting RFID tag with short tag ID, we employ a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in active type RFID.Starting with a short introduction into common RFID systems with passive tags, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications.
Presentation On SECURE SYMMETRIC AUTHENTICATION FOR RFID TAGS DBS INSTITUTE OF TECHNOLOGY Kavali,SPSR Nellore Presented By K.Sandhya, 118T1A0433, ECE.Several authentication schemes have been proposed for providing security in RFID systems. Here, we give a brief review of some protocols. Albert et al.2 use three phases for authentication: initialization, identification (synchronised and desynchronised), and updating phase. This protocol uses the PRNGs to produce an unpredictableStarting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. We demonstrate vulnerabilities of current RFID systems and explain how application of an authentication mechanism can solve them.
tag nfc prix
Secure Symmetric Authentication for RFID Tags
Time, TV schedule. TV Channel: SEC Network. Start time: 11:45 a.m. CT. Auburn vs. ULM will be broadcast nationally on SEC Network in Week 12 of the college football season. Taylor Zarzour and Matt Stinchcomb will call the .
secure symmetric authentication for rfid tags ppt download|Securing IoT