rfid scanner risks Hackers can use RFID scanners to steal money from your phone’s tap-to-pay app, or clone the chip and gain access to a system or data. Additionally, RFID systems are susceptible to passive eavesdropping as well as active interference. Twitter: https://twitter.com/All_HighlytesInstagram: https://www.instagram.com/all_highlytesBusiness Email:
[email protected] rights go to ABC, .
0 · what is rfid security
1 · rfid scam
2 · rfid chip scanning
3 · rfid blocking industry
4 · rfid blockers consumer reports
5 · does rfid blocking hurt
6 · do you need rfid blocking
7 · are rfid tags safe
NFC is short for Near-field communication meaning the cards can be programmed with anything from smart actions, web links to digital profiles and more with friends, colleagues and clients. NFC cards are embedded with tiny .NFL Playoff Picture. Stay up to date with your favorite team to see if they have a chance to make the 2024 playoffs. Seven teams from each conference will make it to the postseason. Check out .
June 9, 2022. Summary: Products such as “RFID wallets” claim to prevent frauds and scams like RFID skimming, in which thieves steal information off your chip-embedded credit card. Be wary of these claims; there are better forms of .

Hackers can use RFID scanners to steal money from your phone’s tap-to-pay app, or clone the chip and gain access to a system or data. Additionally, RFID systems are susceptible to passive eavesdropping as well as active interference.June 9, 2022. Summary: Products such as “RFID wallets” claim to prevent frauds and scams like RFID skimming, in which thieves steal information off your chip-embedded credit card. Be wary of these claims; there are better forms of identity theft . Some people are concerned that attackers could use a handheld device in a crowd to read RFID information from nearby credit cards with contactless payment information embedded in them. Identity thieves could read the same information from an RFID-enabled passport or a security access card with an RFID chip. Passports and some credit cards have RFID chips that allow information to be read wirelessly. An industry has sprung up to make wallets and other products that block hackers from "skimming" the.
First, you need to know how individuals outside of your organization could be accessing your RFID stored data illicitly. Two common methods of this are skimming and eavesdropping: 1. Skimming: To skim is to surreptitiously read a tag, often through the use of a handheld reader. If your system is configured according to a widely used protocol .An RFID virus can either destroy or disclose the tags data stored in the database disrupt the service or block the communication between the database and the reader. To protect your RIFD database, make sure you mitigate database related vulnerabilities and risks.
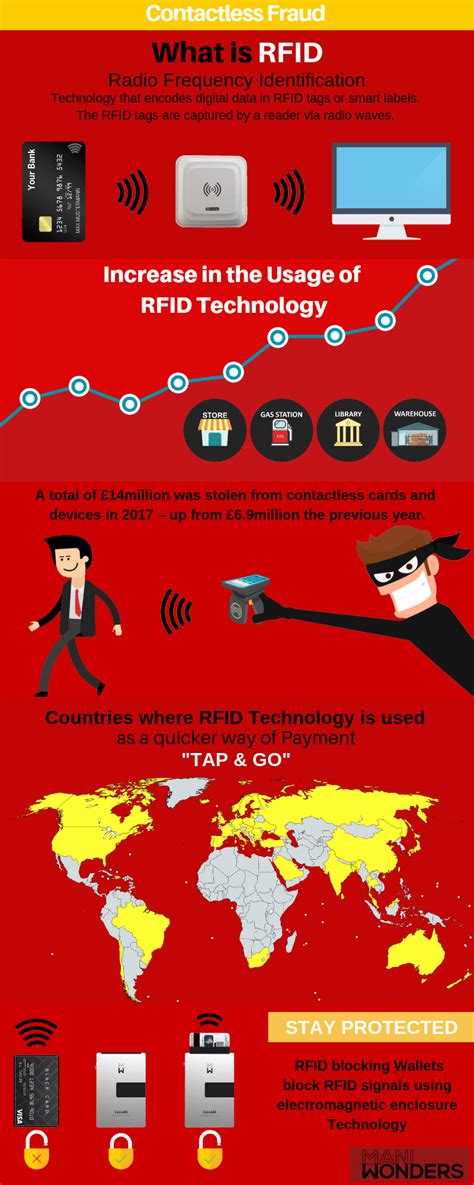
This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks. The infographic below is a handy guide towards understanding RFID skimming and data theft. It will help you understand how hackers can misuse the RFID technology to gain access to your confidential data, increasing the risk of identity thefts and frauds.
Security breaches in RFID systems can have serious consequences, including unauthorized access to sensitive information, theft of valuable assets, and disruption of essential operations. Furthermore, as hackers refine their methods, the risks .
In a previous blog post, we discussed what a radio frequency identification (RFID) access card is, what the risks associated with RFID cards, how to protect yourself when using access cards and why being careful when using RFID cards is important. Hackers can use RFID scanners to steal money from your phone’s tap-to-pay app, or clone the chip and gain access to a system or data. Additionally, RFID systems are susceptible to passive eavesdropping as well as active interference.June 9, 2022. Summary: Products such as “RFID wallets” claim to prevent frauds and scams like RFID skimming, in which thieves steal information off your chip-embedded credit card. Be wary of these claims; there are better forms of identity theft .
Some people are concerned that attackers could use a handheld device in a crowd to read RFID information from nearby credit cards with contactless payment information embedded in them. Identity thieves could read the same information from an RFID-enabled passport or a security access card with an RFID chip. Passports and some credit cards have RFID chips that allow information to be read wirelessly. An industry has sprung up to make wallets and other products that block hackers from "skimming" the. First, you need to know how individuals outside of your organization could be accessing your RFID stored data illicitly. Two common methods of this are skimming and eavesdropping: 1. Skimming: To skim is to surreptitiously read a tag, often through the use of a handheld reader. If your system is configured according to a widely used protocol .An RFID virus can either destroy or disclose the tags data stored in the database disrupt the service or block the communication between the database and the reader. To protect your RIFD database, make sure you mitigate database related vulnerabilities and risks.
This publication seeks to assist organizations in understanding the risks of RFID technology and security measures to mitigate those risks. It provides practical, real-world advice on how to initiate, design, implement and operate RFID systems in a manner that mitigates security and privacy risks. The infographic below is a handy guide towards understanding RFID skimming and data theft. It will help you understand how hackers can misuse the RFID technology to gain access to your confidential data, increasing the risk of identity thefts and frauds.Security breaches in RFID systems can have serious consequences, including unauthorized access to sensitive information, theft of valuable assets, and disruption of essential operations. Furthermore, as hackers refine their methods, the risks .
what is rfid security

gemplus usb smart card reader driver windows 7

hacker.amigo August 22, 2023, 4:37pm #1. Hello, I have read an NFC card from arcade .
rfid scanner risks|rfid blocking industry