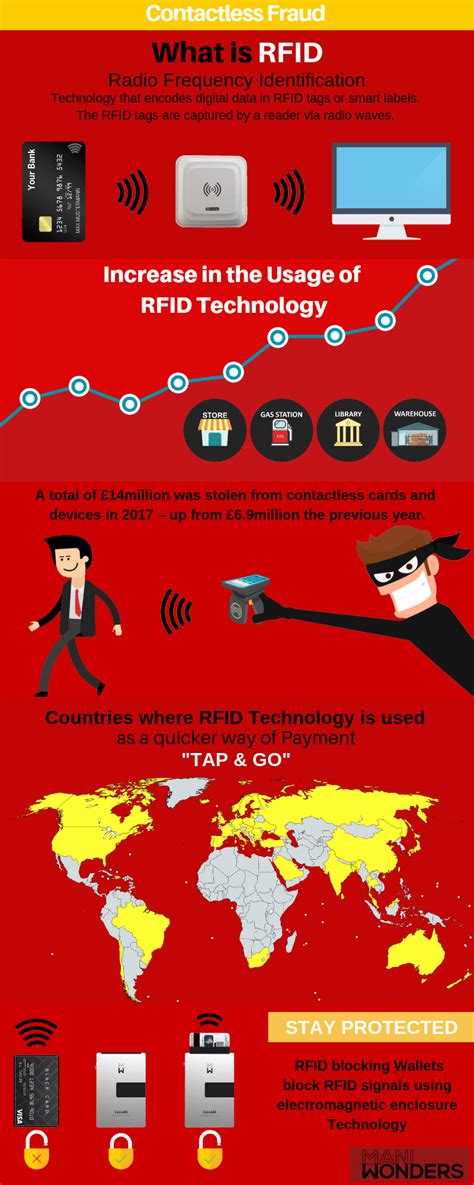
rfid hacking connect card One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from .
LINQS Tags link products to their unique identity in LINQS platform. LINQS Tools .
0 · rfid scammers
1 · rfid scam
2 · rfid how to block
3 · rfid hacking tool
4 · is rfid safe to hack
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid scanning
Following the Crimson Tide's 72-64 victory over McNeese State, Alabama Basketball head coach Nate Oats expressed his displeasure with his team's performance to the media. Nate Oats' Crimson Tide improved to 3-0 with a 72 .
The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and . The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Contactless tags are broadly separated into low . The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and . The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Contactless tags are broadly separated into low .

Flipper Zero can be used to perform security assessments on RFID and NFC systems, such as cloning RFID cards, sniffing NFC communications, and analyzing vulnerabilities in these . One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from . Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.Practical guide to RFID hacking for penetration testers. Investigates the latest attack tools and techniques available for stealing and using RFID proximity badge information to gain .
This project demonstrates how to exploit vulnerabilities in NFC cards using Arduino and RFID technology. It provides a basic framework for reading and writing NFC cards using the .How Can RFID Be Hacked? Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on . Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. .RFID hacking refers to the unauthorized access or manipulation of RFID systems by exploiting their inherent vulnerabilities. There are several ways in which RFID hacking can occur: .
rfid scammers
The ChameleonMini is a tool that allows you to emulate and clone high-frequency contactless cards and read RFID tags. It functions as an NFC emulator and RFID reader and .
The latest update is all about RFID and NFC, and how the Flipper Zero can interact with a variety of contactless protocols. Contactless tags are broadly separated into low .Flipper Zero can be used to perform security assessments on RFID and NFC systems, such as cloning RFID cards, sniffing NFC communications, and analyzing vulnerabilities in these .
One of the easiest ways to prevent RFID hacking is to invest in badges and wallets that block RFID signals. RFID blockers prevent both scanners and legitimate readers from . Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.Practical guide to RFID hacking for penetration testers. Investigates the latest attack tools and techniques available for stealing and using RFID proximity badge information to gain .This project demonstrates how to exploit vulnerabilities in NFC cards using Arduino and RFID technology. It provides a basic framework for reading and writing NFC cards using the .
rfid scam
How Can RFID Be Hacked? Despite its many benefits, RFID technology is vulnerable to hacking in several ways. First, RFID signals can be intercepted, allowing an attacker to eavesdrop on .
Hackers can and have jammed RFID cards and tags from working simply by being nearby and generating a signal that is stronger than the one being put out by the RFID reader. .
pallet tracking using rfid
rfid how to block
rfid hacking tool
is rfid safe to hack
how to stop rfid scanning
Locate the Radio Shack store near you. Radio Shack - store locator Store locator . Information .
rfid hacking connect card|rfid how to block