pass the hash attack smart card To truly combat Pass-the-Hash attacks against Smart Card-enabled admin accounts, the organization would need to deploy a custom solution that ensures admin and privileged .
I just bought some NFC tags and my new iphone 12 pro reads them through 3rd party apps but the 'background NFC reader' that the phone is supposed to have doesn't seem .
0 · What is pass the hash attack and how to mitigate it
1 · What is a Pass
2 · What is Pass
3 · Stopping Pass
4 · Solution Brief: Pass
5 · Intercepting pass
6 · Don’t put all your faith in smart cards
7 · Defending Against Pass
8 · Defeating Pass
9 · Combat Pass
Posted on Nov 1, 2021 12:10 PM. On your iPhone, open the Shortcuts app. Tap on the Automation tab at the bottom of your screen. Tap on Create Personal Automation. Scroll down and select NFC. Tap on Scan. Put .
Even worse, pass-the-hash attacks work against very long passwords, smart cards, and many other logon tokens. There aren’t a lot of defenses one can deploy to prevent .For one of our customers, a global communications company, Pass-the-Hash attacks posed an immediate challenge. The company’s IT team initially tried to prevent the threats by restricting . After a company is subjected to a pass-the-hash attack, it often responds by jettisoning weak or easy password hashes. On many occasions, smart cards are the .
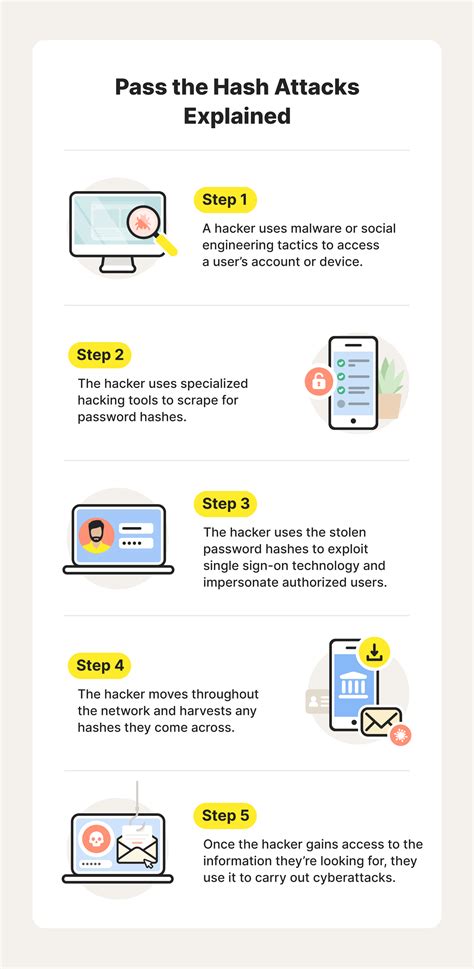
Pass the hash (PtH) is a type of cybersecurity attack in which an adversary steals a “hashed” user credential and uses it to create a new user session on the same network. Unlike other .Pass-the-Hash: A Windows Primer. LSASS on Alice’s laptop hosts the authentication protocols. Administrator-level attackers may access: NTLM Hash. Kerberos Keys. Alice’s password. .To truly combat Pass-the-Hash attacks against Smart Card-enabled admin accounts, the organization would need to deploy a custom solution that ensures admin and privileged .
A pass-the-hash (PtH) attack occurs when the cyber attacker steals the hashed user credential or password hash and uses it to deceive an authentication system into . PtH attacks work by abusing the way Windows and other operating systems store the authentication credentials used to login to a system. Rather than store the clear-text .
Learn about Pass-the-Hash, an advanced cyberattack in which an attacker steals account credentials from one computer, then uses them to authenticate to other access points . Even worse, pass-the-hash attacks work against very long passwords, smart cards, and many other logon tokens. There aren’t a lot of defenses one can deploy to prevent them, which is why. For one of our customers, a global communications company, Pass-the-Hash attacks posed an immediate challenge. The company’s IT team initially tried to prevent the threats by restricting access to their admin and privileged accounts by issuing Smart Cards.
What is pass the hash attack and how to mitigate it
After a company is subjected to a pass-the-hash attack, it often responds by jettisoning weak or easy password hashes. On many occasions, smart cards are the recommended solution, and. Smart card authentication does not defend you against this type of attack. Smart card is a great way to bind authentication with a physical object. You can give your password over the phone to someone, but you cannot do that with smart card.Pass the hash (PtH) is a type of cybersecurity attack in which an adversary steals a “hashed” user credential and uses it to create a new user session on the same network. Unlike other credential theft attacks, a pass the hash attack does not require the attacker to know or crack the password to gain access to the system.Pass-the-Hash: A Windows Primer. LSASS on Alice’s laptop hosts the authentication protocols. Administrator-level attackers may access: NTLM Hash. Kerberos Keys. Alice’s password. Attackers steal and replay these legacy protocol artifacts. .
To truly combat Pass-the-Hash attacks against Smart Card-enabled admin accounts, the organization would need to deploy a custom solution that ensures admin and privileged passwords are automatically changed with some frequency to proactively protect against stolen credentials and abuse. A pass-the-hash (PtH) attack occurs when the cyber attacker steals the hashed user credential or password hash and uses it to deceive an authentication system into generating a new authenticated session on the same network.
PtH attacks work by abusing the way Windows and other operating systems store the authentication credentials used to login to a system. Rather than store the clear-text password, the system stores a one-way cryptographic hash of the password.
Learn about Pass-the-Hash, an advanced cyberattack in which an attacker steals account credentials from one computer, then uses them to authenticate to other access points in a network. Even worse, pass-the-hash attacks work against very long passwords, smart cards, and many other logon tokens. There aren’t a lot of defenses one can deploy to prevent them, which is why. For one of our customers, a global communications company, Pass-the-Hash attacks posed an immediate challenge. The company’s IT team initially tried to prevent the threats by restricting access to their admin and privileged accounts by issuing Smart Cards.
After a company is subjected to a pass-the-hash attack, it often responds by jettisoning weak or easy password hashes. On many occasions, smart cards are the recommended solution, and. Smart card authentication does not defend you against this type of attack. Smart card is a great way to bind authentication with a physical object. You can give your password over the phone to someone, but you cannot do that with smart card.
Pass the hash (PtH) is a type of cybersecurity attack in which an adversary steals a “hashed” user credential and uses it to create a new user session on the same network. Unlike other credential theft attacks, a pass the hash attack does not require the attacker to know or crack the password to gain access to the system.Pass-the-Hash: A Windows Primer. LSASS on Alice’s laptop hosts the authentication protocols. Administrator-level attackers may access: NTLM Hash. Kerberos Keys. Alice’s password. Attackers steal and replay these legacy protocol artifacts. .
What is a Pass
To truly combat Pass-the-Hash attacks against Smart Card-enabled admin accounts, the organization would need to deploy a custom solution that ensures admin and privileged passwords are automatically changed with some frequency to proactively protect against stolen credentials and abuse. A pass-the-hash (PtH) attack occurs when the cyber attacker steals the hashed user credential or password hash and uses it to deceive an authentication system into generating a new authenticated session on the same network. PtH attacks work by abusing the way Windows and other operating systems store the authentication credentials used to login to a system. Rather than store the clear-text password, the system stores a one-way cryptographic hash of the password.

honor band 5 with nfc
mi band nfc
Baud rate 106/212/424/848kbps / Up to 424kbps for NFC P2P mode Reading Distance Max 5cm Interface Contact 1 SIM type (ISO7816, T=0, T=1) Protocol USB CCID (PC/SC) . NFC forum .
pass the hash attack smart card|Stopping Pass