smart card authentication protocol How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to . We’re also excited to announce the Flomio SDK. Now, it’s easy for developers to add NFC to their iOS and Android apps. And together with the . See more
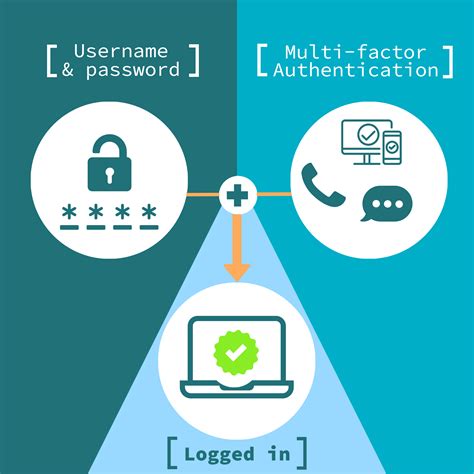
0 · smart card two factor authentication
1 · smart card multi factor authentication
2 · smart card identity
3 · smart card based identification system
4 · smart card authentication step by
5 · enable smart card log on
6 · enable smart card authentication
7 · authenticate using your smart card
Using NFC on Your IPhone. Hold the NFC tag near your iPhone to read it automatically. If you have an older iPhone, open the Control Center and tap the NFC icon. Move the tag over your phone to activate it. The NFC can .
smart card two factor authentication
can rfid's be used as a tracking device
smart card multi factor authentication
Vendors provide smart cards and smart card readers, and in many cases the vendors are different for the smart card and the smart card reader. Drivers for smart . See moreHow Smart Card Sign-in Works in Windows. This topic for IT professional provides links to .Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.
How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. When you use a password to sign in interactively to a domain account, Windows uses the Kerberos version 5 (v5) protocol for authentication. If you use a smart card, the operating system uses Kerberos v5 authentication with X.509 v3 certificates.The CCID (Chip Card Interface Device) is a USB protocol that allows a smart card to be interfaced to a computer using a card reader which has a standard USB interface. This allows the smart card to be used as a security token for authentication and data encryption such as Bitlocker .

Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and industry certifications.The FIDO authentication protocols are designed to allow robust authentication while providing a superior user experience and protecting user privacy. They incorporate the following principles:
rfid conference tracking
All these mechanisms typically focus on the following: Authentication. Access Control. Data Protection. Auditing/Accountability. Authentication is the process by which an entity identifies itself, before network logon is permitted. The process: The user puts the smart card into a card reader hooked up to the device or system they want to use. The card reader talks to the smart card, asking the user to enter a password or give fingerprints to prove who they are.Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and software on the workstation. Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify.
Storing the cryptographic keys in a secure central location makes the authentication process scalable and maintainable. For smart cards, Windows supports a provider architecture that meets the secure authentication requirements and is extensible so that you can include custom credential providers.How Smart Card Sign-in Works in Windows. This topic for IT professional provides links to resources about the implementation of smart card technologies in the Windows operating system. When you use a password to sign in interactively to a domain account, Windows uses the Kerberos version 5 (v5) protocol for authentication. If you use a smart card, the operating system uses Kerberos v5 authentication with X.509 v3 certificates.
The CCID (Chip Card Interface Device) is a USB protocol that allows a smart card to be interfaced to a computer using a card reader which has a standard USB interface. This allows the smart card to be used as a security token for authentication and data encryption such as Bitlocker .
Learn how 1Kosmos enhances smart card authentication with BlockID, offering biometric-based security, identity proofing, privacy by design, distributed ledger technology, interoperability, and industry certifications.
The FIDO authentication protocols are designed to allow robust authentication while providing a superior user experience and protecting user privacy. They incorporate the following principles:
All these mechanisms typically focus on the following: Authentication. Access Control. Data Protection. Auditing/Accountability. Authentication is the process by which an entity identifies itself, before network logon is permitted.
The process: The user puts the smart card into a card reader hooked up to the device or system they want to use. The card reader talks to the smart card, asking the user to enter a password or give fingerprints to prove who they are.Smart Card Authentication is a means of verifying users into enterprise resources such as workstations and applications using a physical card in tandem with a smart card reader and software on the workstation.

The CCID readers below are ideal for MacBooks Pro/Air with Thunderbolt 3/4 or USB-C ports, and the manufacturers provide downloadable drivers for Mac OS. ACS ACR39U-NF fold-away CCID smartcard reader – USB-C. Drivers: PC/SC .
smart card authentication protocol|smart card multi factor authentication