secure symmetric authentication for rfid tags documentation Authentication for Long-range RFID Technology. Feldhofer, M., Dominikus, S. & Aigner, M. J. 1/09/03 → 31/08/05. Project: Research project TIGER TALK. Thursdays at 6 p.m. CT. Hosted by Brad Law and the Voice of the Tigers, Andy Burcham, weekly guests will include head football coach Hugh Freeze in the fall .
0 · Strong Authentication for RFID Systems Using the AES
1 · Secure symmetric authentication for RFID tags
2 · Secure Symmetric Authentication for RFID Tags
3 · Secure Symmetric Authentication for RFID Tags
4 · Secure Symmetric Authentication For Rfid Tags PDF
5 · Research Paper on Secure Symmetric Authentication for RFID
6 · ElProCus
7 · A Secure Authentication Scheme for RFID Systems
November 7, 2024. Throughout the college football season, SiriusXM listeners get access to dozens of game broadcasts each week involving teams from the SEC, Big Ten, Big 12, ACC, and many other conferences across the country. Listen .

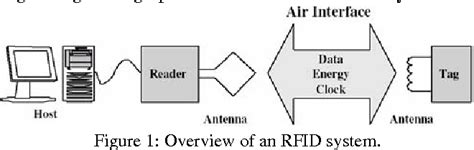
In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is .Starting with a short introduction into common RFID systems with passive tags, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID . Targeting RFID tag with short tag ID, we employ a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in .Authentication for Long-range RFID Technology. Feldhofer, M., Dominikus, S. & Aigner, M. J. 1/09/03 → 31/08/05. Project: Research project
Starting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for .
In contrast to the RFID community, which claims that cryptographic components are too costly for RFID tags, we describe a so-lution using strong symmetric authentication which is suitable for .SECURE-SYMMETRIC-AUTHENTICATION-FOR-RFID-TAGS.pdf - Free download as PDF File (.pdf) or read online for free. Scribd is the world's largest social reading and publishing site.
Several authentication schemes have been proposed for providing security in RFID systems. Here, we give a brief review of some protocols. Albert et al.2 use three phases for . Semantic Scholar extracted view of "Secure Symmetric Authentication for RFID Tags" by Anuj Kumar et al.The project ART proposes to reinforce passive RFID (Radio Frequency Identification) tags with cryptographically secure authentication. beginning with a brief introduction into common RFID .In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners.
Strong Authentication for RFID Systems Using the AES
Starting with a short introduction into common RFID systems with passive tags, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. Targeting RFID tag with short tag ID, we employ a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in active type RFID.Authentication for Long-range RFID Technology. Feldhofer, M., Dominikus, S. & Aigner, M. J. 1/09/03 → 31/08/05. Project: Research project
Starting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. We demonstrate vulnerabilities of current RFID systems and explain how application of an authentication mechanism can solve them.In contrast to the RFID community, which claims that cryptographic components are too costly for RFID tags, we describe a so-lution using strong symmetric authentication which is suitable for today’s requirements regarding low power consumption and low die-size.SECURE-SYMMETRIC-AUTHENTICATION-FOR-RFID-TAGS.pdf - Free download as PDF File (.pdf) or read online for free. Scribd is the world's largest social reading and publishing site.Several authentication schemes have been proposed for providing security in RFID systems. Here, we give a brief review of some protocols. Albert et al.2 use three phases for authentication: initialization, identification (synchronised and desynchronised), and updating phase. This protocol uses the PRNGs to produce an unpredictable
Semantic Scholar extracted view of "Secure Symmetric Authentication for RFID Tags" by Anuj Kumar et al.
The project ART proposes to reinforce passive RFID (Radio Frequency Identification) tags with cryptographically secure authentication. beginning with a brief introduction into common RFID systems with passive tags, we have a tendency to gift a motivation why secure authentication with standardized parallel crypto algorithms for RFID tags is .
In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners.Starting with a short introduction into common RFID systems with passive tags, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications.
use android as nfc card
Targeting RFID tag with short tag ID, we employ a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in active type RFID.Authentication for Long-range RFID Technology. Feldhofer, M., Dominikus, S. & Aigner, M. J. 1/09/03 → 31/08/05. Project: Research projectStarting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. We demonstrate vulnerabilities of current RFID systems and explain how application of an authentication mechanism can solve them.
nfc micro sd card android
In contrast to the RFID community, which claims that cryptographic components are too costly for RFID tags, we describe a so-lution using strong symmetric authentication which is suitable for today’s requirements regarding low power consumption and low die-size.SECURE-SYMMETRIC-AUTHENTICATION-FOR-RFID-TAGS.pdf - Free download as PDF File (.pdf) or read online for free. Scribd is the world's largest social reading and publishing site.Several authentication schemes have been proposed for providing security in RFID systems. Here, we give a brief review of some protocols. Albert et al.2 use three phases for authentication: initialization, identification (synchronised and desynchronised), and updating phase. This protocol uses the PRNGs to produce an unpredictable
Semantic Scholar extracted view of "Secure Symmetric Authentication for RFID Tags" by Anuj Kumar et al.
Secure symmetric authentication for RFID tags
Secure Symmetric Authentication for RFID Tags
The Drive with Bill Cameron, ESPN 106.7’s weekday afternoon sports show, is a fast-paced, in-depth look at the world of sports with a focus on Auburn University and local high schools. Live from 4:00 p.m.-6:00 p.m., the show has been .
secure symmetric authentication for rfid tags documentation|Secure Symmetric Authentication for RFID Tags