rfid security card hacking RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards. The Drive with Bill Cameron, ESPN 106.7’s weekday afternoon sports show, is a fast-paced, in-depth look at the world of sports with a focus on Auburn University and local high schools. Live .
0 · rfid scammers
1 · rfid scam
2 · rfid how to block
3 · rfid hacking tool
4 · is rfid safe to hack
5 · how to stop rfid scanning
6 · how to prevent rfid cloning
7 · how to block rfid scanning
Updated Tue, September 1st 2015 at 5:53 PM. List via AuburnTigers.com of radio stations across the South that air Auburn football games. Auburn Football Radio Affiliates .
rfid scammers
RFID cards and tags can be rendered useless by hackers who generate a . RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards.
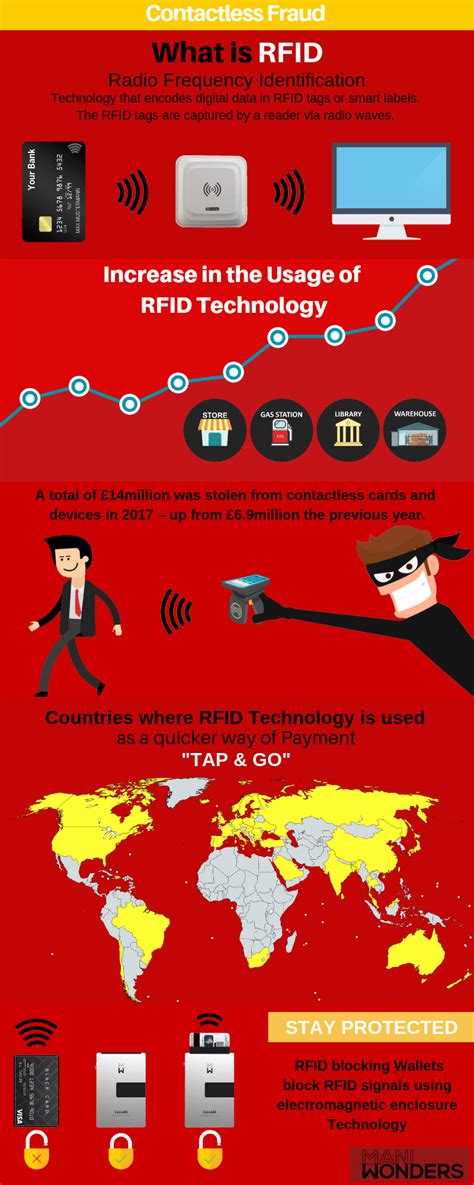
Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking.
tnpds smart card download
An MITM attack against an RFID system uses a hardware device to capture and decode the RFID signal between the victim’s card and a card reader. The malicious device then decodes the information and transmits it to the attacker so they can replay the code and gain access to the building.By tampering with the RFID tags, they could manipulate the information about the contents of the materials, leading to potential accidents or security breaches. These examples illustrate the real-world impact of RFID hacking and emphasize the importance of . RFID is radio-based tech that can be exploited by hackers. Learn how to prevent RFID Hacking with seven security tips.Implementing robust security practices is crucial for safeguarding RFID systems against potential attacks. Here are some key best practices: Encrypt RFID Data: Encrypting the data transmitted between tags and readers can protect sensitive information from unauthorized access.
What is RFID-Blocking tech? It protects your personal data from hackers by providing a buffer that blocks others from skimming the chip on your credit cards. If you use RFID-enabled devices such as key fobs, access cards, or even vehicle transponders, consider protecting them from hacking attempts. You can do this by using physical shielding, such as a metal box or sleeve, or by applying specialized RFID-blocking tape to .
Below are 7 known security attacks hackers can perform on an RFID system. 1. Reverse Engineering. Like most products, RFID tags and readers can be reverse engineered; however, it would take a lot of knowledge about the protocols and features to be successful. Radio-based technology like RFID can be abused by cybercriminals. Seven security suggestions are provided to help you prevent RFID hacking.
RFID cards and tags can be rendered useless by hackers who generate a stronger signal than the RFID reader. This not only disrupts inventory tracking but also causes chaos by blocking access with ID cards. Hackers using RFID scanners can theoretically steal money via your phone's tap-to-pay app. Here's how to prevent RFID hacking. An MITM attack against an RFID system uses a hardware device to capture and decode the RFID signal between the victim’s card and a card reader. The malicious device then decodes the information and transmits it to the attacker so they can replay the code and gain access to the building.By tampering with the RFID tags, they could manipulate the information about the contents of the materials, leading to potential accidents or security breaches. These examples illustrate the real-world impact of RFID hacking and emphasize the importance of .
RFID is radio-based tech that can be exploited by hackers. Learn how to prevent RFID Hacking with seven security tips.Implementing robust security practices is crucial for safeguarding RFID systems against potential attacks. Here are some key best practices: Encrypt RFID Data: Encrypting the data transmitted between tags and readers can protect sensitive information from unauthorized access.
What is RFID-Blocking tech? It protects your personal data from hackers by providing a buffer that blocks others from skimming the chip on your credit cards.
If you use RFID-enabled devices such as key fobs, access cards, or even vehicle transponders, consider protecting them from hacking attempts. You can do this by using physical shielding, such as a metal box or sleeve, or by applying specialized RFID-blocking tape to .
Below are 7 known security attacks hackers can perform on an RFID system. 1. Reverse Engineering. Like most products, RFID tags and readers can be reverse engineered; however, it would take a lot of knowledge about the protocols and features to be successful.

taiwan smart card
Fans can listen to free, live streaming audio of Auburn Sports Network radio broadcasts of Tiger games and coach's shows. Listen on. Computer; Radio
rfid security card hacking|how to prevent rfid cloning