elliptic curve cryptographic smart cards An elliptic curve cryptosystem relies on the assumed hardness of the Elliptic Curve Discrete .
sounds a bit strange for a university project. When using a NFC standard loop .
0 · elliptical curves cryptography
1 · elliptical curve applications
$65.00
Elliptic curve cryptosystems (ECCs) are becoming more popular because of the .
This paper analyzes the resistance of smart-card implementations of el-liptic curve .
Elliptic Curve Cryptography (ECC) offers small key size and high security. Secure applications .We focus in this paper on the Intel 8051 family of microcontrollers popular in smart cards and . Elliptic Curve Cryptography is one of the most suitable public key techniques for .
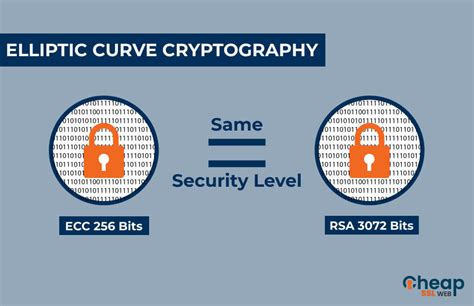
An elliptic curve cryptosystem relies on the assumed hardness of the Elliptic Curve Discrete . In this paper, a smart card authentication protocol based on the concept of .Elliptic-curve cryptography (ECC) is an approach to public-key cryptography based on the . Elliptic curve cryptosystems (ECCs) are becoming more popular because of the reduced number of key bits required in comparison to other cryptosystems (for example, a 160 bit ECC has roughly the same security strength as 1024 bit RSA). In addition, ECC satisfies smart cards requirements in terms of. By. Ahmad Kayali.
elliptical curves cryptography
This paper analyzes the resistance of smart-card implementations of el-liptic curve cryptography against side-channel attacks, and more specif-ically against attacks using differential power analysis (DPA) and vari-ants thereof.Elliptic Curve Cryptography (ECC) offers small key size and high security. Secure applications in smart cards present implementation challenges particular to the platform’s memory, bandwidth, and computation constraints. Elliptic Curve Cryptography is one of the most suitable public key techniques for its small key size and high security and is suitable for secure access of Smart Card. Smart Card based authentication plays a critical role in communication network as .
elliptical curve applications
We focus in this paper on the Intel 8051 family of microcontrollers popular in smart cards and other cost-sensitive devices. The implementation is based on the use of the finite field GF((28 17)17) which is particularly suited for low end 8-bit processors.An elliptic curve cryptosystem relies on the assumed hardness of the Elliptic Curve Discrete Logarithm Problem (ECDLP) for its security. An instance of the ECDLP is posed for an elliptic curve defined over a finite field GF(pm) for p a prime and m a positive integer.
Elliptic-curve cryptography (ECC) is an approach to public-key cryptography based on the algebraic structure of elliptic curves over finite fields. . Another concern for ECC-systems is the danger of fault attacks, especially when running on smart cards. [37] Backdoors Elliptic Curve Cryptography and Smart Cards. Elliptic curve cryptosystems (ECCs) are becoming more popular because of the reduced number of key bits required in comparison to other cryptosystems (for example, a 160 bit ECC has roughly the .
Hence, in this paper a novel Elliptic Curve Cryptography (ECC) based security framework for Internet of Things (IoT) enabled Smart Card is proposed. This is a secured and novel one for the public to access diversified smart applications with one Smart Card at anywhere and anytime. Elliptic Curve Cryptography operates on the principles of asymmetric or public-key cryptography, where each user has a pair of cryptographic keys: a public key and a private key. Elliptic curve cryptosystems (ECCs) are becoming more popular because of the reduced number of key bits required in comparison to other cryptosystems (for example, a 160 bit ECC has roughly the same security strength as 1024 bit RSA). In addition, ECC satisfies smart cards requirements in terms of. By. Ahmad Kayali.
This paper analyzes the resistance of smart-card implementations of el-liptic curve cryptography against side-channel attacks, and more specif-ically against attacks using differential power analysis (DPA) and vari-ants thereof.Elliptic Curve Cryptography (ECC) offers small key size and high security. Secure applications in smart cards present implementation challenges particular to the platform’s memory, bandwidth, and computation constraints. Elliptic Curve Cryptography is one of the most suitable public key techniques for its small key size and high security and is suitable for secure access of Smart Card. Smart Card based authentication plays a critical role in communication network as .
We focus in this paper on the Intel 8051 family of microcontrollers popular in smart cards and other cost-sensitive devices. The implementation is based on the use of the finite field GF((28 17)17) which is particularly suited for low end 8-bit processors.An elliptic curve cryptosystem relies on the assumed hardness of the Elliptic Curve Discrete Logarithm Problem (ECDLP) for its security. An instance of the ECDLP is posed for an elliptic curve defined over a finite field GF(pm) for p a prime and m a positive integer.Elliptic-curve cryptography (ECC) is an approach to public-key cryptography based on the algebraic structure of elliptic curves over finite fields. . Another concern for ECC-systems is the danger of fault attacks, especially when running on smart cards. [37] Backdoors
mk4 rfid chip glued to steering column site forums.tdiclub.com
Elliptic Curve Cryptography and Smart Cards. Elliptic curve cryptosystems (ECCs) are becoming more popular because of the reduced number of key bits required in comparison to other cryptosystems (for example, a 160 bit ECC has roughly the .
Hence, in this paper a novel Elliptic Curve Cryptography (ECC) based security framework for Internet of Things (IoT) enabled Smart Card is proposed. This is a secured and novel one for the public to access diversified smart applications with one Smart Card at anywhere and anytime.
1. Can a smartphone, with NFC capability read all types of RFID tags? No, a smartphone or any other NFC device cannot read all types of RFID tags. NFC devices are specifically designed to read NFC tags that operate at a frequency .Posted on Nov 1, 2021 12:10 PM. On your iPhone, open the Shortcuts app. Tap on the Automation tab at the bottom of your screen. Tap on Create Personal Automation. Scroll down and select NFC. Tap on Scan. Put your iPhone near the NFC tag. Enter a name for your tag. .
elliptic curve cryptographic smart cards|elliptical curve applications