mifare classic tool copy my bank card Go to Applications - NFC Magic and run it. You need RW NFC tags. Got some very cheap from ebay and they work fine. Check magic tag with app to make sure you have a compatible Gen1A tag. Optional - use WIPE function to clear the tag/card. Ultraman Geed Complete. Topics Tokusatsu Item Size 15.5G . Geed Addeddate 2023-07-30 18:29:46 Identifier ultraman-geed-all Scanner Internet Archive HTML5 Uploader 1.7.0 . plus-circle Add .
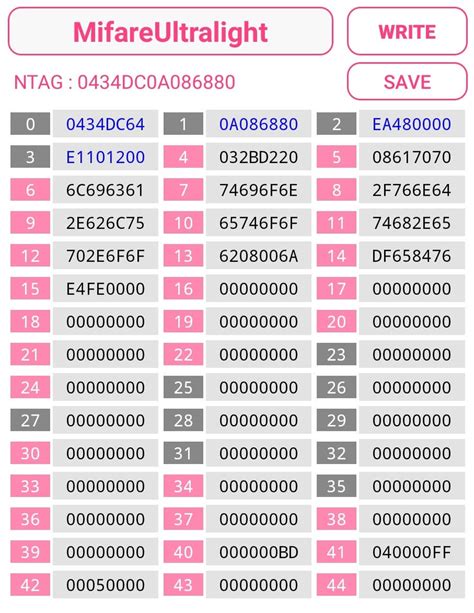
0 · mifare ultralight uid card
1 · mifare ultralight card clone
2 · mifare card clone code
Start the amiibo-compatible game and follow the on-screen instructions. Please note that you .
I tried the exact thing some time ago, purchased a MIFARE card with writable sector 0 and tried cloning it with MIFARE classic tool. Did not work, I think it was due to the uni-card being encrypted. The MIFARE classic tool on the Play Store can't bruteforce cards if I remember . Go to Applications - NFC Magic and run it. You need RW NFC tags. Got some very cheap from ebay and they work fine. Check magic tag with app to make sure you have a . I tried the exact thing some time ago, purchased a MIFARE card with writable sector 0 and tried cloning it with MIFARE classic tool. Did not work, I think it was due to the uni-card being encrypted. The MIFARE classic tool on the Play Store can't bruteforce cards if I remember correctly. Go to Applications - NFC Magic and run it. You need RW NFC tags. Got some very cheap from ebay and they work fine. Check magic tag with app to make sure you have a compatible Gen1A tag. Optional - use WIPE function to clear the tag/card.
I autopwn my current fob, it found keys and saved 64 blocks to text file /Users/home/hf-mf-B3929B7F-dump-006.eml. I also used autopwn on the new key card and its saved the keys to: hf-mf-B3929B7F-key-003.bin. I tired cload and got the error below, and tried restore but the card still doesn’t work. As it is just cool to write a cards dump back, I have found a 4Byte UID MIFARE Classic 1kB card. Card information Content of Sector: 0 . Ebay has a solution for everyting. UID writable MIFARE Classic cards. These cards make it possible to write Sector 0 – block 0 (i.e. the manufacturer block).
If you want a clone of the card then you want both the UID and the data on the card to be copied across to the new card, but this isn’t normally possible due to the UID being read only. Enter the “UID changeable”, aka “Chinese backdoor” (seriously) cards, which allow you to change their UID.
Here’s how you can clone Mifare NFC Classic 1K Cards using an Android smartphone with NFC capabilities. That’s right. You can use your cell phone to compromise the security of a company if they are using these types of cards. In this post I will share how to clone a MiFare Classic card using the Proxmark 3 Easy. Requirements: Hardware . Proxmark3 Easy ; Software. The RRG / Iceman git repo (found here: https://github.com/RfidResearchGroup/proxmark3) Process: Obtain keys. Default keys ; Non-default keys; Dump card content; Write dump to empty card; Obtains keysThe Proxmark3 is used to show how to clone a Mifare Classic card and the NFC/RFID security of smart cards is discussed. Episode 4 of Proxmark 3 Basics: Learn how to identify, crack, read and clone MIFARE Classic® cards. The Proxmark 3 RDV4.01 main firmware branches integrate all known MIFARE Classic® cracking techniques, and this episode deep dives into each one.
Due to some weaknesses in MIFARE Classic, you can retrieve all the keys (A and B) of a tag with tools like the Proxmark3 or normal RFID-Readers and some special software (mfcuk, mfoc). The application comes with standard key files called std.keys and extended-std.keys , which contain the well known keys and some standard keys from a short . I tried the exact thing some time ago, purchased a MIFARE card with writable sector 0 and tried cloning it with MIFARE classic tool. Did not work, I think it was due to the uni-card being encrypted. The MIFARE classic tool on the Play Store can't bruteforce cards if I remember correctly. Go to Applications - NFC Magic and run it. You need RW NFC tags. Got some very cheap from ebay and they work fine. Check magic tag with app to make sure you have a compatible Gen1A tag. Optional - use WIPE function to clear the tag/card. I autopwn my current fob, it found keys and saved 64 blocks to text file /Users/home/hf-mf-B3929B7F-dump-006.eml. I also used autopwn on the new key card and its saved the keys to: hf-mf-B3929B7F-key-003.bin. I tired cload and got the error below, and tried restore but the card still doesn’t work.
As it is just cool to write a cards dump back, I have found a 4Byte UID MIFARE Classic 1kB card. Card information Content of Sector: 0 . Ebay has a solution for everyting. UID writable MIFARE Classic cards. These cards make it possible to write Sector 0 – block 0 (i.e. the manufacturer block).
If you want a clone of the card then you want both the UID and the data on the card to be copied across to the new card, but this isn’t normally possible due to the UID being read only. Enter the “UID changeable”, aka “Chinese backdoor” (seriously) cards, which allow you to change their UID. Here’s how you can clone Mifare NFC Classic 1K Cards using an Android smartphone with NFC capabilities. That’s right. You can use your cell phone to compromise the security of a company if they are using these types of cards. In this post I will share how to clone a MiFare Classic card using the Proxmark 3 Easy. Requirements: Hardware . Proxmark3 Easy ; Software. The RRG / Iceman git repo (found here: https://github.com/RfidResearchGroup/proxmark3) Process: Obtain keys. Default keys ; Non-default keys; Dump card content; Write dump to empty card; Obtains keysThe Proxmark3 is used to show how to clone a Mifare Classic card and the NFC/RFID security of smart cards is discussed.
Episode 4 of Proxmark 3 Basics: Learn how to identify, crack, read and clone MIFARE Classic® cards. The Proxmark 3 RDV4.01 main firmware branches integrate all known MIFARE Classic® cracking techniques, and this episode deep dives into each one.
how do i remove nfc tag reader

mifare ultralight uid card
mifare ultralight card clone
REACT NFC Sample App. This is a simple sample app demostrating the usage of the NFC API. To get the NFC API working you will need an Android Device with Google Chrome and your web app will .
mifare classic tool copy my bank card|mifare ultralight uid card