rfid security systems How to become a cloud security engineer: Job opportunities, skills and more Nearly 100 zettabytes of data will be stored in the cloud by 2025. That means pursuing a career in cloud security is a pretty safe choice.
Developers use the iOS Core NFC Framework to add NFC functionality to their apps. Both foreground and Background NFC Tags Reading functionality can be implemented in 3rd party apps. 3rd party apps which use NFC break down .
0 · what is the best rfid blocking method
1 · rfid technology pros and cons
2 · rfid systems for small business
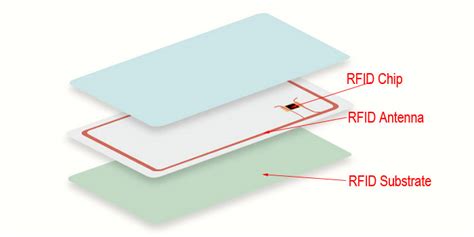
3 · rfid card what is it
4 · rfid based tracking system
5 · rfid based location tracking system
6 · best rfid access control system
7 · 10 door access control system
Find out more info about OnePlus 9 Pro:https://www.hardreset.info/devices/oneplus/oneplus-9-pro/Do you want to start using the OnePlus 9 Pro for contactless .The Opal card uses near field communication (NFC) technology that allows users to tap on and .
An RFID access control system is a security management system based on radio frequency . Learn how to design, implement and operate RFID systems that mitigate security .- Security monitoring - Log aggregation - Log collectors • Security orchestration, automation, and response (SOAR) Explain the techniques used in penetration testing. Summarize the techniques used in security assessments. 1.8 1.7 1.0 Threats, Attacks, and Vulnerabilities CompTIA Security+ Certification Exam Objectives Version 3.0 (Exam Number .About the Exam. date has the knowledge and skills required to:Assess the security posture of an enterprise environment and recommen. and implement appropriate security solutions.Monitor and secure hybrid environments, includ. g cloud, mobile, and Internet of Things (IoT).Operate with an awareness of applicable regulations and policies, including.
Network security. A deep dive into network security protocols: Safeguarding digital infrastructure 2024. Explore the vital role of network security protocols in safeguarding digital infrastructure in 2024, covering types, trends and best practices.How to become a cloud security engineer: Job opportunities, skills and more Nearly 100 zettabytes of data will be stored in the cloud by 2025. That means pursuing a career in cloud security is a pretty safe choice.
Master the art of security architecture with Infosec Skills. Learn to design, implement, and maintain robust security solutions.gain in-depth knowledge of security governance, risk management, security program development and management, and security incident management. The boot camp has been updated to align with the new CISM job practice areas and is designed to fully prepare you to pass the challenging CISM exam. Who should attend » Information security managers Mid-level security engineer roles & responsibilities . As a mid-level security engineer, your roles and responsibilities will grow into more of the management end of cybersecurity. In addition to what was expected of you as a beginner security engineer, mid-level security engineers will have the following responsibilities: Developing threat models A systems administrator helps manage the configuration and operation of various IT systems, servers and networks. As more systems have moved to the cloud, some job roles specialize in cloud admin and security, and some have a mix. Common certifications for these types of roles include: Red Hat Certified System Administrator (RHCSA): Validates .
» Security managers and leaders » Anyone interested in builiding their skills as an analyst Analyze data to identify vulnerabilities, threats and risks Configure and use threat detection tools Secure and protect applications and systems Immediate access to Infosec Skills 5-day boot camp 90-day extended access to all boot camp materialsAI is poised to be an increasingly effective resource for providing IoT security at scale. Security engineers can take a single AI-powered solution and duplicate it in multiple environments. For example, suppose a company adds a satellite location that .- Security monitoring - Log aggregation - Log collectors • Security orchestration, automation, and response (SOAR) Explain the techniques used in penetration testing. Summarize the techniques used in security assessments. 1.8 1.7 1.0 Threats, Attacks, and Vulnerabilities CompTIA Security+ Certification Exam Objectives Version 3.0 (Exam Number .About the Exam. date has the knowledge and skills required to:Assess the security posture of an enterprise environment and recommen. and implement appropriate security solutions.Monitor and secure hybrid environments, includ. g cloud, mobile, and Internet of Things (IoT).Operate with an awareness of applicable regulations and policies, including.
Network security. A deep dive into network security protocols: Safeguarding digital infrastructure 2024. Explore the vital role of network security protocols in safeguarding digital infrastructure in 2024, covering types, trends and best practices.
what is the best rfid blocking method

rfid technology pros and cons
How to become a cloud security engineer: Job opportunities, skills and more Nearly 100 zettabytes of data will be stored in the cloud by 2025. That means pursuing a career in cloud security is a pretty safe choice.Master the art of security architecture with Infosec Skills. Learn to design, implement, and maintain robust security solutions.

gain in-depth knowledge of security governance, risk management, security program development and management, and security incident management. The boot camp has been updated to align with the new CISM job practice areas and is designed to fully prepare you to pass the challenging CISM exam. Who should attend » Information security managers
Mid-level security engineer roles & responsibilities . As a mid-level security engineer, your roles and responsibilities will grow into more of the management end of cybersecurity. In addition to what was expected of you as a beginner security engineer, mid-level security engineers will have the following responsibilities: Developing threat models A systems administrator helps manage the configuration and operation of various IT systems, servers and networks. As more systems have moved to the cloud, some job roles specialize in cloud admin and security, and some have a mix. Common certifications for these types of roles include: Red Hat Certified System Administrator (RHCSA): Validates .» Security managers and leaders » Anyone interested in builiding their skills as an analyst Analyze data to identify vulnerabilities, threats and risks Configure and use threat detection tools Secure and protect applications and systems Immediate access to Infosec Skills 5-day boot camp 90-day extended access to all boot camp materials

rfid systems for small business
use of rfid tags in library
All said and done, activity tag in your android manifest file should look something like this : You’re all set to handle the intents in your activity now! Step 1. Create an instance of NfcAdapter and initialise it in the onCreate ( ) .
rfid security systems|what is the best rfid blocking method