smart card access control method Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify. 1409 Fourth Avenue. Sidney, OH 45365. M.E.L.S Back to the 50's Drive-in. 8721 N. State Road 39. Thorntown, IN 46071. The Auburn Garrett Drive-in is a single screen drive-in theater opened in 1951. It is located in Garrett, IN. Check here .
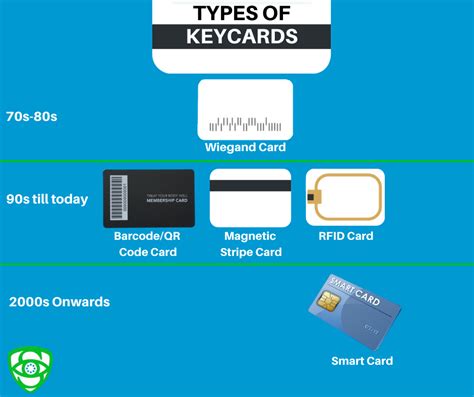
0 · types of access control cards
1 · smart card door access system
2 · smart card access control systems
3 · identisys swipe access card
4 · hid card access control system
5 · hid access control system installation
6 · hid access card log in
7 · employee door access control
The NFL Playoff Schedule for the 2018 season kicks off on Saturday with two Wild-Card Round games, followed by two more Wild-Card games on .
Smart cards, and other related devices, may be used to provide an increased level of security in applications requiring controlled access to sensitive information. This publication describes the basic components of a smart card, and the goals and obstacles of smart card application .Smart cards, and other related devices, may be used to provide an increased level of security in applications requiring controlled access to sensitive information. This publication describes the basic components of a smart card, and the goals and obstacles of .Smart cards offer enhanced security and convenience, making them ideal for various applications, including secure transactions, access control, and identification purposes. 30 to 50B smart cards in circulation today Smart cards can process data, carry out commands, and secure information thanks to recent advancements in circuit chip technology. In this comprehensive guide, we’ll dive into different types of smart cards for access control, their functionalities, and their uses in .
Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify.

Access control is not just about allowing or denying access. It involves identifying an individual or system, authenticating their identity, authorizing them to access the resource, and auditing their access patterns. This process minimizes the risk of unauthorized access, protecting sensitive information and systems.Smart cards contain an embedded chip used as either a microprocessor or memory, which create some complications in implementing smart cards for network access. Centralization and distribution access control models are most appropriate for smart cards.
Smart cards implement three levels of logical access control. The first level includes the association of a set of privileges with a user's password and the ability to control access to.The Secure Technology Alliance is a not-for-profit, multi-industry association working to stimulate the understanding, adoption, and widespread application of secure solutions, including smart cards, embedded chip technology, and related hardware and software across a variety of markets including authentication, commerce, and Internet of Things . Smart Cards for Access Control Advantages and Technology Choices. Posted date: 12 Jul 2021. Download. Language.Learn all about smart card access control systems in our detailed guide and find out what type of smart card door access systems are best for you.
types of access control cards
Smart cards, and other related devices, may be used to provide an increased level of security in applications requiring controlled access to sensitive information. This publication describes the basic components of a smart card, and the goals and obstacles of .Smart cards offer enhanced security and convenience, making them ideal for various applications, including secure transactions, access control, and identification purposes. 30 to 50B smart cards in circulation today Smart cards can process data, carry out commands, and secure information thanks to recent advancements in circuit chip technology. In this comprehensive guide, we’ll dive into different types of smart cards for access control, their functionalities, and their uses in .
Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify. Access control is not just about allowing or denying access. It involves identifying an individual or system, authenticating their identity, authorizing them to access the resource, and auditing their access patterns. This process minimizes the risk of unauthorized access, protecting sensitive information and systems.Smart cards contain an embedded chip used as either a microprocessor or memory, which create some complications in implementing smart cards for network access. Centralization and distribution access control models are most appropriate for smart cards. Smart cards implement three levels of logical access control. The first level includes the association of a set of privileges with a user's password and the ability to control access to.
The Secure Technology Alliance is a not-for-profit, multi-industry association working to stimulate the understanding, adoption, and widespread application of secure solutions, including smart cards, embedded chip technology, and related hardware and software across a variety of markets including authentication, commerce, and Internet of Things .
Smart Cards for Access Control Advantages and Technology Choices. Posted date: 12 Jul 2021. Download. Language.
how do i turn off nfc tag not supported
emvco approved nfc tag
smart card door access system
smart card access control systems
Harvey Updyke, the Alabama football fan who made national headlines when he poisoned trees at Auburn University’s Toomer’s Corner in 2010, has died. His son Bear Updyke told AL.com that his .
smart card access control method|identisys swipe access card