biometrics include physical credentials such as smart cards and barcodes. Unlike traditional methods involving passwords or tokens, biometric data is an inherent part of the user and cannot be easily lost, stolen, or forgotten. Enhanced User . Near-Field Communication (NFC) is a radio-based contactless peer-to-peer communication protocol for exchange between devices at very close distances.NFC can be used to read tags and for Apple Pay. To use, make sure your iPhone is unlocked, and then tap the top of your iPhone's back on the tag to get a pop-up. Unfortunately, it seems NFC on iPhone cannot be used to connect to bluetooth, so you cannot use NFC to .Download the Apps and you are good to go. If you don't have the XS, XS Max or XR, then to read NFC tags, you need to have installed iOS 11 or later and will need an App. NFC tag scanning with an App is only available on the iPhone 7, iPhone 7 Plus, iPhone 8, iPhone 8 .
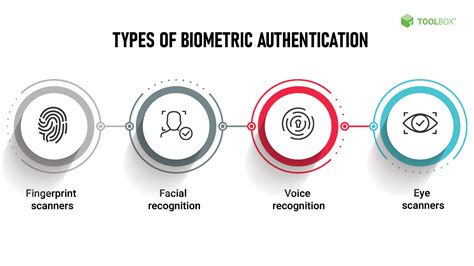
0 · what is biometric identification
1 · what is a biometric person
2 · what is a biometric characteristic
3 · examples of biometrics
4 · definition of biometrics
5 · biometric personality identification
Game: Time (ET) SiriusXM Channels: Wisconsin vs. Alabama: 12 p.m. 195 (Wisconsin), 82 (Alabama) South Carolina vs. LSU: 12 p.m. 374 (South Carolina), 191 (LSU)
Study with Quizlet and memorize flashcards containing terms like Biometrics include physical credentials such as smart cards and barcodes., The companies that make antivirus software .Biometrics include physical credentials such as smart cards and barcodes. False. Which of the following is a common type of software bug that can be exploited to compromise the security .Study with Quizlet and memorize flashcards containing terms like Biometrics include physical credentials such as smart cards and barcodes., The companies that make antivirus software . Unlike traditional methods involving passwords or tokens, biometric data is an inherent part of the user and cannot be easily lost, stolen, or forgotten. Enhanced User .
Biometrics include physical credentials such as smart cards and barcodes. False. Which of the following is a common type of software bug that can be exploited to compromise the security .Biometrics are automated methods of recognizing a person based on a physiological or behavioral char-acteristic. Biometric technologies are becoming the foundation of an extensive .
Unlike conventional biometric processes, the "Match-on-Card" algorithm allows fingerprints to be matched locally with a reference frame thanks to a microprocessor built into . Biometrics are physical or behavioral human characteristics to that can be used to digitally identify a person to grant access to systems, devices, or data. Examples of these .

Biometrics can be used to identify you as you. Tokens, such as smart cards, magnetic stripe cards, photo ID cards, physical keys and so forth, can be lost, stolen, duplicated, or left at home. Examples include biometrics data, biographic data and relational data (work history, family, and addresses). A credential is a physical or logical binding of identity to .Using biometrics for identifying human beings offers some unique advantages. Biometrics can be used to identify you as you. Tokens, such as smart cards, magnetic stripe cards, photo ID .
Biometrics refers to the measurement and statistical analysis of a person’s unique physical characteristics. The technology is primarily used for identification and access control, .Study with Quizlet and memorize flashcards containing terms like Biometrics include physical credentials such as smart cards and barcodes., The companies that make antivirus software . Unlike traditional methods involving passwords or tokens, biometric data is an inherent part of the user and cannot be easily lost, stolen, or forgotten. Enhanced User .
Biometrics include physical credentials such as smart cards and barcodes. False. Which of the following is a common type of software bug that can be exploited to compromise the security .Biometrics are automated methods of recognizing a person based on a physiological or behavioral char-acteristic. Biometric technologies are becoming the foundation of an extensive .

Unlike conventional biometric processes, the "Match-on-Card" algorithm allows fingerprints to be matched locally with a reference frame thanks to a microprocessor built into .
Biometrics are physical or behavioral human characteristics to that can be used to digitally identify a person to grant access to systems, devices, or data. Examples of these .Biometrics can be used to identify you as you. Tokens, such as smart cards, magnetic stripe cards, photo ID cards, physical keys and so forth, can be lost, stolen, duplicated, or left at home. Examples include biometrics data, biographic data and relational data (work history, family, and addresses). A credential is a physical or logical binding of identity to .
what is biometric identification
Using biometrics for identifying human beings offers some unique advantages. Biometrics can be used to identify you as you. Tokens, such as smart cards, magnetic stripe cards, photo ID .
what is a biometric person
Step 1: Open the Shortcuts app > go to the Automation tab. Step 2: Tap New Automation or + (from the top-right corner). Step 3: Here, scroll down or search for NFC. Tap it. Step 4: Tap Scan. Hold .
biometrics include physical credentials such as smart cards and barcodes.|examples of biometrics