server 2008 smart card exploit This policy setting determines what happens when the smart card for a logged-on user is removed from the smart card reader. If smart cards are used for authentication, the .
Get an unlocked rooted android and flash custom firmware like a Hacker OS so it can do more .
0 · Windows Smart Card Authentication Exploitation
1 · Top 20 Critical Windows Server 2008 Vulnerabilities
2 · Microsoft RDP Bug Enables Data Theft, Smart
3 · Microsoft Operating Systems BlueKeep Vulnerability
4 · Interactive logon: Smart card removal behavior
5 · Heads up: Total Meltdown exploit code now available on GitHub
6 · Government cybersecurity agency warns of Windows Server exploit
7 · Ekultek/BlueKeep: Proof of concept for CVE
8 · Attacking smart cards in active directory
9 · Attacking RDP from Inside: How we abused named pipes for smar
The NFC TagWriter by NXP stores contacts, bookmarks, geo location, Bluetooth Handover, SMS, Mail, text messages and many more to .
A tool released in this dump is “EsteemAudit”, which exploits CVE-2017–9073, a vulnerability in the Windows Remote Desktop system on Windows XP and Windows Server .
Bluekeep or CVE-2019-0708 is an RCE exploit that effects the following versions of Windows systems: Windows 2003; Windows XP; Windows Vista; Windows 7; Windows Server 2008; Windows Server 2008 R2; The vulnerability occurs .
Windows Smart Card Authentication Exploitation
Top 20 Critical Windows Server 2008 Vulnerabilities
Enable Network Level Authentication in Windows 7, Windows Server 2008, and Windows Server 2008 R2. Doing so forces a session request to be authenticated and . The massive security hole introduced by Microsoft for 64-bit Win7 and Server 2008 R2 now has working proof-of-concept code — and it’s freely available on GitHub. First one, try to attack the smart card directly by forging a certificate with an arbitrary SAN. Unless you have a way to break RSA you should not be able to do this. This policy setting determines what happens when the smart card for a logged-on user is removed from the smart card reader. If smart cards are used for authentication, the .
Rare warning from CISA instructs government agencies to patch a vulnerability in a core authentication component of Active Directory from Windows Server 2008 to Windows . CyberArk developed a simple exploit tool that creates its own pipe server instance and showed how an attacker could use it to access the file system of the victim, intercept .Learn about the top 20 Windows Server 2008 vulnerabilities, exploits, and security flaws that can lead to a data breach and how to fix them. Video 3: Smart Card Redirection. Summary. This vulnerability shows an example of an unconventional attack vector targeting RDP. Instead of tapping into the input side of the server/client as one usually does, we abused the RDP server internal mechanism as an entry point. We chose to focus on drive and smart card redirection.
A tool released in this dump is “EsteemAudit”, which exploits CVE-2017–9073, a vulnerability in the Windows Remote Desktop system on Windows XP and Windows Server 2003. The vulnerability .Bluekeep or CVE-2019-0708 is an RCE exploit that effects the following versions of Windows systems: Windows 2003; Windows XP; Windows Vista; Windows 7; Windows Server 2008; Windows Server 2008 R2; The vulnerability occurs during pre-authorization and has the potential to run arbitrary malicious code in the NT Authority\system user security context. Enable Network Level Authentication in Windows 7, Windows Server 2008, and Windows Server 2008 R2. Doing so forces a session request to be authenticated and effectively mitigates against BlueKeep, as exploit of the vulnerability requires an unauthenticated session.
The massive security hole introduced by Microsoft for 64-bit Win7 and Server 2008 R2 now has working proof-of-concept code — and it’s freely available on GitHub. First one, try to attack the smart card directly by forging a certificate with an arbitrary SAN. Unless you have a way to break RSA you should not be able to do this. This policy setting determines what happens when the smart card for a logged-on user is removed from the smart card reader. If smart cards are used for authentication, the computer should automatically lock itself when the card is removed—that way, if users forget to manually lock their workstations when they are away from them, malicious .
Rare warning from CISA instructs government agencies to patch a vulnerability in a core authentication component of Active Directory from Windows Server 2008 to Windows Server 2019. CyberArk developed a simple exploit tool that creates its own pipe server instance and showed how an attacker could use it to access the file system of the victim, intercept whatever the victim.Learn about the top 20 Windows Server 2008 vulnerabilities, exploits, and security flaws that can lead to a data breach and how to fix them. Video 3: Smart Card Redirection. Summary. This vulnerability shows an example of an unconventional attack vector targeting RDP. Instead of tapping into the input side of the server/client as one usually does, we abused the RDP server internal mechanism as an entry point. We chose to focus on drive and smart card redirection.
Microsoft RDP Bug Enables Data Theft, Smart
A tool released in this dump is “EsteemAudit”, which exploits CVE-2017–9073, a vulnerability in the Windows Remote Desktop system on Windows XP and Windows Server 2003. The vulnerability .Bluekeep or CVE-2019-0708 is an RCE exploit that effects the following versions of Windows systems: Windows 2003; Windows XP; Windows Vista; Windows 7; Windows Server 2008; Windows Server 2008 R2; The vulnerability occurs during pre-authorization and has the potential to run arbitrary malicious code in the NT Authority\system user security context. Enable Network Level Authentication in Windows 7, Windows Server 2008, and Windows Server 2008 R2. Doing so forces a session request to be authenticated and effectively mitigates against BlueKeep, as exploit of the vulnerability requires an unauthenticated session. The massive security hole introduced by Microsoft for 64-bit Win7 and Server 2008 R2 now has working proof-of-concept code — and it’s freely available on GitHub.
First one, try to attack the smart card directly by forging a certificate with an arbitrary SAN. Unless you have a way to break RSA you should not be able to do this. This policy setting determines what happens when the smart card for a logged-on user is removed from the smart card reader. If smart cards are used for authentication, the computer should automatically lock itself when the card is removed—that way, if users forget to manually lock their workstations when they are away from them, malicious .
Rare warning from CISA instructs government agencies to patch a vulnerability in a core authentication component of Active Directory from Windows Server 2008 to Windows Server 2019.
CyberArk developed a simple exploit tool that creates its own pipe server instance and showed how an attacker could use it to access the file system of the victim, intercept whatever the victim.

Microsoft Operating Systems BlueKeep Vulnerability

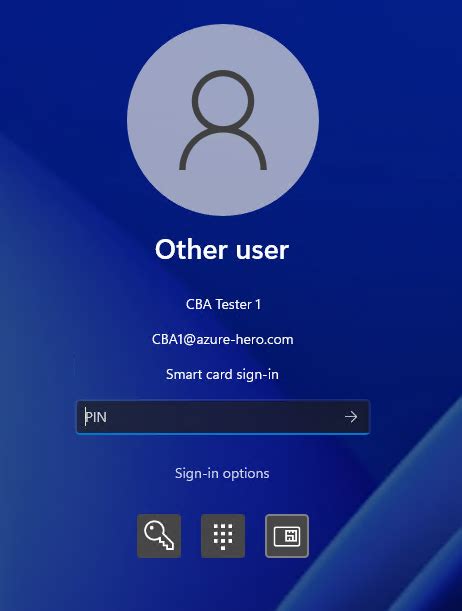
Interactive logon: Smart card removal behavior
Heads up: Total Meltdown exploit code now available on GitHub
Government cybersecurity agency warns of Windows Server exploit
NFC Tools is an app which allows you to read, write and program tasks on your NFC tags and other compatible NFC chips. Simple and intuitive, NFC Tools can record standard information on your NFC tags which will be .
server 2008 smart card exploit|Microsoft RDP Bug Enables Data Theft, Smart