smart card security tokens All tokens contain some secret information used to prove identity. There are four different ways in which this information can be used:Static password token The device contains a password that is . See more An NFC card is most commonly made of white PVC, but can also be made of wood, colored PVC or metal. They are waterproof, durable and slightly thicker than a credit card. By default NFC cards are a standard CR80 size but can be made larger or in custom shapes and can have one or more punched holes or slots.
0 · what is smart card number
1 · what is smart card authentication
2 · smart card identity
3 · smart card identification
4 · smart card based identification system
5 · smart card based authentication
6 · memory based smart card
7 · azure smart card authentication
$14.99
what is smart card number
A security token is a peripheral device used to gain access to an electronically restricted resource. The token is used in addition to, or in place of, a password. Examples of security tokens include wireless key cards used to open locked doors, a banking token used as a digital authenticator for signing in to . See moreAll tokens contain some secret information used to prove identity. There are four different ways in which this information can be used:Static password token The device contains a password that is . See more
what is smart card authentication
Loss and theftThe simplest vulnerability with any password container is theft or loss of the device. The chances . See more
• Authentication• Authenticator• Hardware security module• Identity management• Initiative for Open Authentication See more
• Media related to OTP tokens at Wikimedia Commons• OATH Initiative for open authentication Archived 2019-04-24 at the Wayback Machine See more
Tokens can contain chips with functions varying from very simple to very complex, including multiple authentication methods.The simplest security tokens do not need any connection to a computer. The tokens have a physical display; the authenticating user simply enters . See more
Trusted as a regular hand-written signature, the digital signature must be made with a private key known only to the person authorized to make the signature. Tokens that allow secure on-board generation and storage of private keys enable secure . See moreA security token is a peripheral device used to gain access to an electronically restricted resource. The token is used in addition to, or in place of, a password.
Smart cards offer more security and confidentiality than other financial information or transaction storage vehicles, making them a perfect solution for e-commerce transactions.
smart card identity
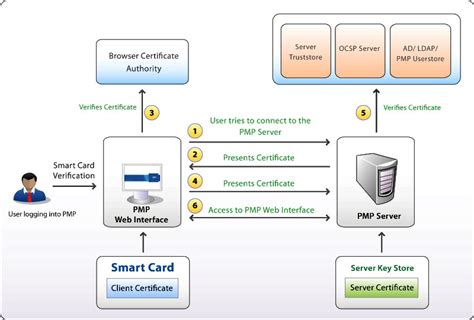
Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify. Smart-card-based USB tokens which contain a smart card chip inside provide the functionality of both USB tokens and smart cards. They enable a broad range of security solutions and provide the abilities and security of a traditional .This new edition adds content on RFIDs, embedded security, attacks and countermeasures, security evaluation, javacards, banking or payment cards, identity cards and passports, mobile systems security, and security management. A step-by-step approach educates the reader in card types, production, operating systems, commercial applications, new .presents the main features of smart card technology in the light of the EMV card specifications. The discussion continues with 3D secure and token authentication.

Smart Cards, Tokens, Security and Applications. K. Mayes, K. Markantonakis. Published 18 October 2010. Computer Science. TLDR. This state-of-the art work combines a cross-discipline overview of smart cards, tokens and related security and applications plus a technical reference to support further research and study. Expand. View via Publisher. Smart Cards, Tokens, Security and Applications provides a broad overview of the many card systems and solutions that are in practical use today. This state-of-the art work is written by. This book combines a cross-discipline overview of smart cards, tokens and related security and applications plus a technical reference to support further research and study.
This new edition adds content on RFIDs, embedded security, attacks and countermeasures, security evaluation, javacards, banking or payment cards, identity cards and passports, mobile systems security, and security management.
A security token is a peripheral device used to gain access to an electronically restricted resource. The token is used in addition to, or in place of, a password.
Smart cards offer more security and confidentiality than other financial information or transaction storage vehicles, making them a perfect solution for e-commerce transactions. Smart card authentication is a method that employs the embedded chip in the card to verify the identity of the user certificates. The chip can generate or store authentication data through cryptographic algorithms that a reader can verify. Smart-card-based USB tokens which contain a smart card chip inside provide the functionality of both USB tokens and smart cards. They enable a broad range of security solutions and provide the abilities and security of a traditional .This new edition adds content on RFIDs, embedded security, attacks and countermeasures, security evaluation, javacards, banking or payment cards, identity cards and passports, mobile systems security, and security management. A step-by-step approach educates the reader in card types, production, operating systems, commercial applications, new .
presents the main features of smart card technology in the light of the EMV card specifications. The discussion continues with 3D secure and token authentication. Smart Cards, Tokens, Security and Applications. K. Mayes, K. Markantonakis. Published 18 October 2010. Computer Science. TLDR. This state-of-the art work combines a cross-discipline overview of smart cards, tokens and related security and applications plus a technical reference to support further research and study. Expand. View via Publisher.
Smart Cards, Tokens, Security and Applications provides a broad overview of the many card systems and solutions that are in practical use today. This state-of-the art work is written by. This book combines a cross-discipline overview of smart cards, tokens and related security and applications plus a technical reference to support further research and study.
convert rc book to smart card chennai
smart card identification
smart card based identification system
smart card based authentication
Fans can listen to free, live streaming audio of Auburn Sports Network radio broadcasts of Tiger games and coach's shows. Computer; Mobile App; Radio; TuneIn Opens in a new window ; Audio.Statewide coverage is the hallmark of the Auburn Sports Network's exclusive coverage of Auburn football. All home and away games are broadcast across the entire state of Alabama plus portions of .
smart card security tokens|smart card based authentication