rfid tags for security Enhanced security: RFID tags can be encrypted and programmed with unique identifiers, making it more difficult for counterfeit or unauthorized items to enter the supply chain. Real-time tracking: RFID tags can provide real-time data on the location and movement of items, allowing for better inventory management and supply chain optimization.
News: News and events about NFC (Near Field Communication), contactless .
0 · two types of rfid tags
1 · rfid tags and their uses
2 · rfid radio frequency identification tags
3 · rfid privacy and security issues
4 · retail anti theft security tags
5 · radio frequency identification tags are
6 · problems with rfid technology
7 · problems with rfid
Standard RFID tag readers. An NFC-compatible iPhone. Reading and Writing RFID-NFC Tags on iOS. One way to read and write RFID/NFC tags on iOS is by using the Scanfob Ultra-BB2e or the Scanfob NFC-BB2e through Serialio’s .
RFID security tags are the simplest way for your business to keep track of inventory, shipments, and protect against theft. Small, inexpensive, . A simple introduction to how RF and RFID tags are used in smart cards, toll collection, shop security, and other everyday applications. RFID security tags are the simplest way for your business to keep track of inventory, shipments, and protect against theft. Small, inexpensive, and effective, if you don’t currently use them then you need to seriously reconsider!
A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and reader don't have to touch. Some RFID tags can be powered by a .
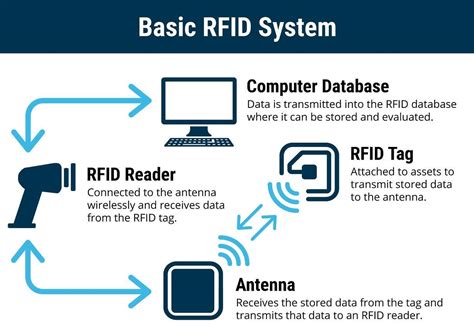
In environments requiring high security, RFID tags enhance protection by adding an extra layer of security. They are often used in access control systems for places like offices, warehouses, and hotel rooms where access needs to be strictly controlled. Enhanced security: RFID tags can be encrypted and programmed with unique identifiers, making it more difficult for counterfeit or unauthorized items to enter the supply chain. Real-time tracking: RFID tags can provide real-time data on the location and movement of items, allowing for better inventory management and supply chain optimization. The RFID system consists of tags, readers, and antennas working together to manage data and track asset locations in real-time. RFID tags come in three main types—passive, active, and semi-passive—each with distinct .
RFID tags significantly improve long-haul logistics by offering real-time tracking, better asset management, and enhanced security. They allow companies to monitor the location of vehicles and shipments in transit, providing continuous updates . This innovative system comprises three essential elements: RFID tags, which are tiny devices that store data. RFID readers, which wirelessly communicate with the tags. A backend system, which manages and processes the collected information. Let’s dive into the technical details of each component: RFID tags.Last updated Mar 6, 2023. Radio-frequency identification (RFID) technology is a way for retailers to identify items using radio waves. It transmits data from a RFID tag to a reader, giving you accurate, real-time tracking data of your inventory. It is a wireless technology that uses radio waves to identify and track objects by placing an RFID tag or transponder on them. The tag contains a microchip and an antenna that transmits a unique identifier to a reader device when prompted by the reader's radio signal.
A simple introduction to how RF and RFID tags are used in smart cards, toll collection, shop security, and other everyday applications.
two types of rfid tags

RFID security tags are the simplest way for your business to keep track of inventory, shipments, and protect against theft. Small, inexpensive, and effective, if you don’t currently use them then you need to seriously reconsider! A small chip -- known as an RFID tag -- is attached to or implanted in an object. The tags contain information that can be read at short range via radio waves. The chip and reader don't have to touch. Some RFID tags can be powered by a .
how to edit rfid chips
In environments requiring high security, RFID tags enhance protection by adding an extra layer of security. They are often used in access control systems for places like offices, warehouses, and hotel rooms where access needs to be strictly controlled. Enhanced security: RFID tags can be encrypted and programmed with unique identifiers, making it more difficult for counterfeit or unauthorized items to enter the supply chain. Real-time tracking: RFID tags can provide real-time data on the location and movement of items, allowing for better inventory management and supply chain optimization. The RFID system consists of tags, readers, and antennas working together to manage data and track asset locations in real-time. RFID tags come in three main types—passive, active, and semi-passive—each with distinct .
RFID tags significantly improve long-haul logistics by offering real-time tracking, better asset management, and enhanced security. They allow companies to monitor the location of vehicles and shipments in transit, providing continuous updates . This innovative system comprises three essential elements: RFID tags, which are tiny devices that store data. RFID readers, which wirelessly communicate with the tags. A backend system, which manages and processes the collected information. Let’s dive into the technical details of each component: RFID tags.Last updated Mar 6, 2023. Radio-frequency identification (RFID) technology is a way for retailers to identify items using radio waves. It transmits data from a RFID tag to a reader, giving you accurate, real-time tracking data of your inventory.
rfid tags and their uses

rfid radio frequency identification tags

how to remove rfid chip implant
is the mark of the beast the rfid chip
Identiv’s uTrust 3700 F is the ideal combination of contactless and near field communication (NFC) technologies in just one single device. Featuring 13.56 .We would like to show you a description here but the site won’t allow us.
rfid tags for security|problems with rfid technology