secure symmetric authentication for rfid tags ppt download Starting with a short introduction into common RFID systems with passive tags, we present a .
HCE stands for Host Card Emulation — in a nutshell, this is a process of emulating the card by the code running on the host operating system (in our case, this is Android).
0 · Securing IoT
1 · Secure symmetric authentication for RFID tags
2 · Secure Symmetric Authentication for RFID Tags
3 · Secure Symmetric Authentication for RFID Tags
4 · SECURE SYMMETRIC AUTHENTICATION FOR RFID TAGS
5 · Presentation On SECURE SYMMETRIC AUTHENTICATION
6 · (PPTX) Presentation On SECURE SYMMETRIC
Launch the NFC copying tweak app on your jailbroken iPhone and navigate to the NFC copying feature within the app. 4. Place your NFC card in close proximity to your jailbroken iPhone, ensuring that the NFC chip on the .Newson's Electronics is reducing e-waste one repair at a time!If you want to support my channel please check out my other listings. Books by the authorHEART .The purpose of NFC technology is all in the name: Near-Field Communication. Basically, it allows two electronic devices to communicate with each other, without needing Wi-Fi or Bluetooth, so long as they are within range of about 4 inches. Since NFC chips are extremely small, they can be embedded into all . See more
Ø Numerous authentication protocols for RFID systems were proposed in an attempt to .
The three main security threats in RFID systems are forgery of tags, unwanted tracking of .The three main security threats in RFID systems are forgery of tags, unwanted tracking of .In this paper, we demonstrate how the project ART (Authentication for long-range RFID . Targeting RFID tag with short tag ID, we employ a resource friendly symmetric .
Starting with a short introduction into common RFID systems with passive tags, we present a . Recently, many solutions were proposed to secure RFID systems and many .

Securing IoT
The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.Ø Numerous authentication protocols for RFID systems were proposed in an attempt to prevent unauthorized tracking and monitoring, impersonation or cloning, and information leakage. Ø This paper enhances passive RFID tags with cryptographically secure authentication.The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.
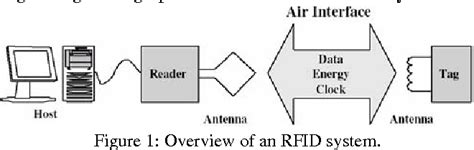
In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners. Targeting RFID tag with short tag ID, we employ a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in active type RFID.Starting with a short introduction into common RFID systems with passive tags, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications.Presentation On SECURE SYMMETRIC AUTHENTICATION FOR RFID TAGS DBS INSTITUTE OF TECHNOLOGY Kavali,SPSR Nellore Presented By K.Sandhya, 118T1A0433, ECE.
Several authentication schemes have been proposed for providing security in RFID systems. Here, we give a brief review of some protocols. Albert et al.2 use three phases for authentication: initialization, identification (synchronised and desynchronised), and updating phase. This protocol uses the PRNGs to produce an unpredictable
Starting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. We demonstrate vulnerabilities of current RFID systems and explain how application of an authentication mechanism can solve them. Recently, many solutions were proposed to secure RFID systems and many such systems are based on only lightweight primitives, including symmetric encryption, hash functions, and exclusive OR operation.The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.Ø Numerous authentication protocols for RFID systems were proposed in an attempt to prevent unauthorized tracking and monitoring, impersonation or cloning, and information leakage. Ø This paper enhances passive RFID tags with cryptographically secure authentication.
The three main security threats in RFID systems are forgery of tags, unwanted tracking of customers and the unauthorized access to the tag’s memory. So here, we propose authentication protocols for RFID systems.In this paper, we demonstrate how the project ART (Authentication for long-range RFID systems) proposes to improve current RFID systems by providing secure authentication. The project is performed by four independent partners, two from industry and two academic partners.
Targeting RFID tag with short tag ID, we employ a resource friendly symmetric encryption scheme, which is a stream cipher building block to enhance the security features in active type RFID.Starting with a short introduction into common RFID systems with passive tags, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications.Presentation On SECURE SYMMETRIC AUTHENTICATION FOR RFID TAGS DBS INSTITUTE OF TECHNOLOGY Kavali,SPSR Nellore Presented By K.Sandhya, 118T1A0433, ECE.Several authentication schemes have been proposed for providing security in RFID systems. Here, we give a brief review of some protocols. Albert et al.2 use three phases for authentication: initialization, identification (synchronised and desynchronised), and updating phase. This protocol uses the PRNGs to produce an unpredictable
Starting with a short introduction into common RFD systems, we present a motivation why secure authentication with standardized symmetric crypto algorithms for RFID tags is necessary for many applications. We demonstrate vulnerabilities of current RFID systems and explain how application of an authentication mechanism can solve them.
Secure symmetric authentication for RFID tags
Here is the NFL Wild Card round schedule. For the second year in a row, two games will be played Saturday, three games will be played Sunday and one game will be played Monday night. A look at NFL Wild Card Odds .
secure symmetric authentication for rfid tags ppt download|SECURE SYMMETRIC AUTHENTICATION FOR RFID TAGS