smart lte sim card hack Host and manage packages Security. Find and fix vulnerabilities OEM Contactless Unattended Reader Features and Benefits . Felica, NFC, ISO15693. . UIC .
0 · sim card identity hacking
1 · sim card hacking scam
2 · sim card hacked pin code
3 · sim card hacked
4 · how to secure your sim card
5 · how to prevent sim card hacking
6 · how to hack your sim card
7 · how to check if sim card is hacked
$13.17
LTE/LTE-A Jamming, Spoofing, and Sniffing - Assessment and Mitigation; Exploring LTE security and protocol exploits with open source software and low-cost software radio by Roger Jover; .Issues 2 - W00t3k/Awesome-Cellular-Hacking: Awesome-Cellular-Hacking - .Pull requests - W00t3k/Awesome-Cellular-Hacking: Awesome-Cellular-Hacking - .Actions - W00t3k/Awesome-Cellular-Hacking: Awesome-Cellular-Hacking - .
Host and manage packages Security. Find and fix vulnerabilities
We would like to show you a description here but the site won’t allow us.Activity - W00t3k/Awesome-Cellular-Hacking: Awesome-Cellular-Hacking - . SIM swapping (or SIM jacking) is one of the nastier hacks you can fall victim too. It essentially reroutes your cell number to another SIM, and another phone. Scammers can use your SIM card to make calls, send SMS messages, and post to social media accounts on your behalf. Hijacking your phone number may be the first step .
LTE/LTE-A Jamming, Spoofing, and Sniffing - Assessment and Mitigation; Exploring LTE security and protocol exploits with open source software and low-cost software radio by Roger Jover; LTE PROTOCOL EXPLOITS: IMSI CATCHERS,BLOCKING DEVICES AND LOCATION LEAKS; Practical Attacks Against Privacy and Availability in 4G/LTE Mobile Communication Systems SIM swapping (or SIM jacking) is one of the nastier hacks you can fall victim too. It essentially reroutes your cell number to another SIM, and another phone. Here's how hackers use SIM cards to gain access to devices, and how to keep your SIM card safe. 1. Simjacker Attacks. In September 2019, security researchers at AdaptiveMobile Security announced they had discovered a new security vulnerability they called Simjacker. Scammers can use your SIM card to make calls, send SMS messages, and post to social media accounts on your behalf. Hijacking your phone number may be the first step towards completely taking over your digital life.
rfid animal tag
SIM swap fraud exploits this by deceiving carriers into transferring a mobile number from its owner's device to another device with a different SIM card. Transferring the number sends calls, voicemails, and texts to the new device rather than the owner's device.Hacking Public Warning System in LTE Mobile Networks. Rooting SIM-cards. RF Exploitation: IoT/OT Hacking with SDR. Forcing a targeted LTE Cellphone Into an Eavesdropping Network. Hacking Cellular Networks. Bye-Bye-IMSI-Catchers. New Privacy Threat on 3G, 4G, and Upcoming 5G AKA Protocols. Recognizing the signs of a potential SIM card hack, such as unexpected disruptions in services, unexplained account changes, and unusual battery performance, empowers individuals to promptly address suspicions and mitigate the potential impact of these security breaches.
A 0 million lawsuit against AT&T. A bustling underground crime ring. They all have roots in an old problem that has lately found new urgency: SIM card swaps, a scam in which hackers steal your. 1. To be able to use mobile data (e.g. 4G/ LTE) and mobile telephony (e.g. VoLTE) services on my smartphone, I need to put a SIM card into my smartphone (I know embedded-SIM/ eSIM exists but let's ignore that here). This SIM card is provided to me by a mobile network operator or mobile virtual network operator. Learn how to identify signs of a hacked SIM card and protect your mobile device from security breaches. Understand the warning signals and take necessary precautions.
LTE/LTE-A Jamming, Spoofing, and Sniffing - Assessment and Mitigation; Exploring LTE security and protocol exploits with open source software and low-cost software radio by Roger Jover; LTE PROTOCOL EXPLOITS: IMSI CATCHERS,BLOCKING DEVICES AND LOCATION LEAKS; Practical Attacks Against Privacy and Availability in 4G/LTE Mobile Communication Systems
SIM swapping (or SIM jacking) is one of the nastier hacks you can fall victim too. It essentially reroutes your cell number to another SIM, and another phone. Here's how hackers use SIM cards to gain access to devices, and how to keep your SIM card safe. 1. Simjacker Attacks. In September 2019, security researchers at AdaptiveMobile Security announced they had discovered a new security vulnerability they called Simjacker. Scammers can use your SIM card to make calls, send SMS messages, and post to social media accounts on your behalf. Hijacking your phone number may be the first step towards completely taking over your digital life. SIM swap fraud exploits this by deceiving carriers into transferring a mobile number from its owner's device to another device with a different SIM card. Transferring the number sends calls, voicemails, and texts to the new device rather than the owner's device.
Hacking Public Warning System in LTE Mobile Networks. Rooting SIM-cards. RF Exploitation: IoT/OT Hacking with SDR. Forcing a targeted LTE Cellphone Into an Eavesdropping Network. Hacking Cellular Networks. Bye-Bye-IMSI-Catchers. New Privacy Threat on 3G, 4G, and Upcoming 5G AKA Protocols. Recognizing the signs of a potential SIM card hack, such as unexpected disruptions in services, unexplained account changes, and unusual battery performance, empowers individuals to promptly address suspicions and mitigate the potential impact of these security breaches. A 0 million lawsuit against AT&T. A bustling underground crime ring. They all have roots in an old problem that has lately found new urgency: SIM card swaps, a scam in which hackers steal your.
sim card identity hacking
sim card hacking scam
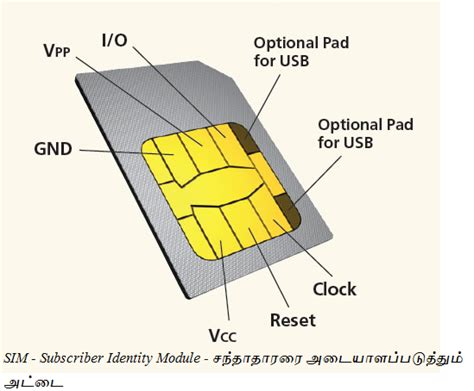
1. To be able to use mobile data (e.g. 4G/ LTE) and mobile telephony (e.g. VoLTE) services on my smartphone, I need to put a SIM card into my smartphone (I know embedded-SIM/ eSIM exists but let's ignore that here). This SIM card is provided to me by a mobile network operator or mobile virtual network operator.
passive rfid labels
Check whether your smartphone is compatible with NFC. What is an NFC compatible smartphone? NOTE: If you want to use NFC with an iPhone, you will need an iPhone 7 or later .Broke-ed_Pancreas. •. The PDM is essentially a locked down phone. All phones will generally create a response if it has an NFC reader. .
smart lte sim card hack|how to prevent sim card hacking